v1.5.2
Documentation & Examples
Downloads for v1.5.2
| filename |
sha256 hash |
| kubernetes.tar.gz |
67344958325a70348db5c4e35e59f9c3552232cdc34defb8a0a799ed91c671a3 |
| kubernetes-src.tar.gz |
93241d0f7b69de71d68384699b225ed8a5439bde03dc154827a2b7a6a343791e |
Client Binaries
Server Binaries
Changelog since v1.5.1
Other notable changes
- Fixes NotAuthenticated errors that appear in the kubelet and kube-controller-manager due to never logging in to vSphere (#36169, @robdaemon)
- Update amd64 kube-proxy base image to debian-iptables-amd64:v5 (#39725, @ixdy)
- Update kube-proxy image to be based off of Debian 8.6 base image. (#39695, @ixdy)
- Fixes an HPA-related panic due to division-by-zero. (#39694, @DirectXMan12)
- Update fluentd-gcp addon to 1.28.1 (#39706, @ixdy)
- Provide kubernetes-controller-manager flags to control volume attach/detach reconciler sync. The duration of the syncs can be controlled, and the syncs can be shut off as well. (#39551, @chrislovecnm)
- AWS: Recognize ca-central-1 region (#38410, @justinsb)
- fix nil dereference when doing a volume type check on persistent volumes (#39529, @sjenning)
- Generate OpenAPI definition for inlined types (#39466, @mbohlool)
- Admit critical pods in the kubelet (#38836, @bprashanth)
- assign -998 as the oom_score_adj for critical pods (e.g. kube-proxy) (#39114, @dchen1107)
- Don't evict static pods (#39059, @bprashanth)
- Fix an issue where AWS tear-down leaks an DHCP Option Set. (#38645, @zmerlynn)
- Give apply the versioned struct that generated from the type defined in the restmapping. (#38982, @ymqytw)
- Add support for Azure Container Registry, update Azure dependencies (#37783, @brendandburns)
- Fixes an issue where
hack/local-up-cluster.sh would fail on the API server start with (#38898, @deads2k)
- Since
kubernetes.tar.gz no longer includes client or server binaries, cluster/kube-{up,down,push}.sh now automatically download released binaries if they are missing. (#38730, @ixdy)
- Fixed validation of multizone cluster for GCE (#38695, @jszczepkowski)
- Fix nil pointer dereference in test framework (#37583, @mtaufen)
- Fixed detection of master during creation of multizone nodes cluster by kube-up. (#38617, @jszczepkowski)
- Kubelet: Add image cache. (#38375, @Random-Liu)
v1.4.8
Documentation & Examples
Downloads for v1.4.8
| filename |
sha256 hash |
| kubernetes.tar.gz |
888d2e6c5136e8805805498729a1da55cf89addfd28f098e0d2cf3f28697ab5c |
| kubernetes-src.tar.gz |
0992c3f4f4cb21011fea32187c909babc1a3806f35cec86aacfe9c3d8bef2485 |
Client Binaries
Server Binaries
Changelog since v1.4.7
Other notable changes
- AWS: recognize eu-west-2 region (#38746, @justinsb)
- Add path exist check in getPodVolumePathListFromDisk (#38909, @jingxu97)
- Update fluentd-gcp addon to 1.21.1/1.25.1. (#39705, @ixdy)
- Admit critical pods in the kubelet (#38836, @bprashanth)
- assign -998 as the oom_score_adj for critical pods (e.g. kube-proxy) (#39114, @dchen1107)
- Don't evict static pods (#39059, @bprashanth)
- Provide kubernetes-controller-manager flags to control volume attach/detach reconciler sync. The duration of the syncs can be controlled, and the syncs can be shut off as well. (#39551, @chrislovecnm)
- AWS: Recognize ca-central-1 region (#38410, @justinsb)
- Add TLS conf for Go1.7 (#38600, @k82cn)
- Fix fsGroup to vSphere (#38655, @abrarshivani)
- Only set sysctls for infra containers (#32383, @sttts)
- fix kubectl taint e2e flake: add retries for removing taint (#33872, @kevin-wangzefeng)
- portfordwardtester: avoid data loss during send+close+exit (#37103, @sttts)
- Wait for the port to be ready before starting (#38260, @fraenkel)
- Ensure the GCI metadata files do not have newline at the end (#38727, @Amey-D)
- Fix nil pointer dereference in test framework (#37583, @mtaufen)
- Kubelet: Add image cache. (#38375, @Random-Liu)
- Collect logs for dead kubelets too (#37671, @mtaufen)
v1.5.1
Documentation & Examples
Downloads for v1.5.1
| filename |
sha256 hash |
| kubernetes.tar.gz |
adc4f6ec1fc8f97ed19f474ffcc0af2d050f92dc20ecec2799741802019205ec |
| kubernetes-src.tar.gz |
27e5009b906b9f233a7be1efcf51140be945446d828c006c171d03fe07e43565 |
Client Binaries
Server Binaries
Changelog since v1.5.0
Other notable changes
Known Issues for v1.5.1
hack/local-up-cluster.sh script times out waiting for apiserver to answer, see #38847.
To workaround this, modify the script to pass --anonymous-auth=true to sudo -E "${GO_OUT}/hyperkube" apiserver ... when starting kube-apiserver.
v1.5.0
Documentation & Examples
Downloads for v1.5.0
| filename |
sha256 hash |
| kubernetes.tar.gz |
52b7df98ea05fb3ebbababf1ccb7f6d4e6f4cad00b8d09350f270aa7e3ad7e85 |
| kubernetes-src.tar.gz |
fbefb2544667f96045c346cee595b0f315282dfdbd41a8f2d5ccc74054a4078e |
Client Binaries
Server Binaries
Major Themes
- StatefulSets (ex-PetSets)
- StatefulSets are beta now (fixes and stabilization)
- Improved Federation Support
- New command:
kubefed
- DaemonSets
- Deployments
- ConfigMaps
- Simplified Cluster Deployment
- Improvements to
kubeadm
- HA Setup for Master
- Node Robustness and Extensibility
- Windows Server Container support
- CRI for pluggable container runtimes
kubelet API supports authentication and authorization
Features
Features for this release were tracked via the use of the kubernetes/features issues repo. Each Feature issue is owned by a Special Interest Group from kubernetes/community
- API Machinery
- Apps
- [stable] When replica sets cannot create pods, they will now report detail via the API about the underlying reason (kubernetes/features#120)
- [stable]
kubectl apply is now able to delete resources you no longer need with --prune (kubernetes/features#128)
- [beta] Deployments that cannot make progress in rolling out the newest version will now indicate via the API they are blocked (docs) (kubernetes/features#122)
- [beta] StatefulSets allow workloads that require persistent identity or per-instance storage to be created and managed on Kubernetes. (docs) (kubernetes/features#137)
- [beta] In order to preserve safety guarantees the cluster no longer force deletes pods on un-responsive nodes and users are now warned if they try to force delete pods via the CLI. (docs) (kubernetes/features#119)
- Auth
- AWS
- Cluster Lifecycle
- Cluster Ops
- [alpha] Added ability to create/remove clusters w/highly available (replicated) masters on GCE using kube-up/kube-down scripts. (docs) (kubernetes/features#48)
- Federation
- Network
- [stable] Services can reference another service by DNS name, rather than being hosted in pods (kubernetes/features#33)
- [beta] Opt in source ip preservation for Services with Type NodePort or LoadBalancer (docs) (kubernetes/features#27)
- [stable] Enable DNS Horizontal Autoscaling with beta ConfigMap parameters support (docs)
- Node
- [alpha] Added ability to preserve access to host userns when userns remapping is enabled in container runtime (kubernetes/features#127)
- [alpha] Introducing the v1alpha1 CRI API to allow pluggable container runtimes; an experimental docker-CRI integration is ready for testing and feedback. (docs) (kubernetes/features#54)
- [alpha] Kubelet launches container in a per pod cgroup hiearchy based on quality of service tier (kubernetes/features#126)
- [beta] Kubelet integrates with memcg notification API to detect when a hard eviction threshold is crossed (kubernetes/features#125)
- [beta] Introducing the beta version containerized node conformance test gcr.io/google_containers/node-test:0.2 for users to verify node setup. (docs) (kubernetes/features#84)
- Scheduling
- UI
- Windows
Known Issues
Populated via v1.5.0 known issues / FAQ accumulator
Notable Changes to Existing Behavior
-
Node controller no longer force-deletes pods from the api-server. ([#35235](https://github.com/kubernetes/kubernetes/pull/35235), [@foxish](https://github.com/foxish))
- For StatefulSet (previously PetSet), this change means creation of
replacement pods is blocked until old pods are definitely not running
(indicated either by the kubelet returning from partitioned state,
deletion of the Node object, deletion of the instance in the cloud provider,
or force deletion of the pod from the api-server).
This helps prevent "split brain" scenarios in clustered applications by
ensuring that unreachable pods will not be presumed dead unless some
"fencing" operation has provided one of the above indications.
- For all other existing controllers except StatefulSet, this has no effect on
the ability of the controller to replace pods because the controllers do not
reuse pod names (they use generate-name).
- User-written controllers that reuse names of pod objects should evaluate this change.
- When deleting an object with
kubectl delete ... --grace-period=0, the client will
begin a graceful deletion and wait until the resource is fully deleted. To force
deletion immediately, use the --force flag. This prevents users from accidentally
allowing two Stateful Set pods to share the same persistent volume which could lead to data
corruption [#37263](https://github.com/kubernetes/kubernetes/pull/37263)
-
Allow anonymous API server access, decorate authenticated users with system:authenticated group ([#32386](https://github.com/kubernetes/kubernetes/pull/32386), [@liggitt](https://github.com/liggitt))
- kube-apiserver learned the '--anonymous-auth' flag, which defaults to true. When enabled, requests to the secure port that are not rejected by other configured authentication methods are treated as anonymous requests, and given a username of 'system:anonymous' and a group of 'system:unauthenticated'.
- Authenticated users are decorated with a 'system:authenticated' group.
- IMPORTANT: See Action Required for important actions related to this change.
-
kubectl get -o jsonpath=... will now throw an error if the path is to a field not present in the json, even if the path is for a field valid for the type. This is a change from the pre-1.5 behavior, which would return the default value for some fields even if they were not present in the json. ([#37991](https://github.com/kubernetes/kubernetes/issues/37991), [@pwittrock](http://github.com/pwittrock))
-
The strategicmerge patchMergeKey for VolumeMounts was changed from "name" to "mountPath". This was necessary because the name field refers to the name of the Volume, and is not a unique key for the VolumeMount. Multiple VolumeMounts will have the same Volume name if mounting the same volume more than once. The "mountPath" is verified to be unique and can act as the mergekey. ([#35071](https://github.coma/kubernetes/kubernetes/pull/35071), [@pwittrock](http://github.com/pwittrock))
Deprecations
Action Required Before Upgrading
- **Important Security-related changes before upgrading
- You MUST set
--anonymous-auth=false flag on your kube-apiserver unless you are a developer testing this feature and understand it.
If you do not, you risk allowing unauthorized users to access your apiserver.
- You MUST set
--anonymous-auth=false flag on your federation apiserver unless you are a developer testing this feature and understand it.
If you do not, you risk allowing unauthorized users to access your federation apiserver.
- You do not need to adjust this flag on Kubelet: there was no authorization for the Kubelet APIs in 1.4.
- batch/v2alpha1.ScheduledJob has been renamed, use batch/v2alpha1.CronJob instead ([#36021](https://github.com/kubernetes/kubernetes/pull/36021), [@soltysh](https://github.com/soltysh))
- PetSet has been renamed to StatefulSet.
If you have existing PetSets, you must perform extra migration steps both
before and after upgrading to convert them to StatefulSets. (docs) ([#35663](https://github.com/kubernetes/kubernetes/pull/35663), [@janetkuo](https://github.com/janetkuo))
- If you are upgrading your Cluster Federation components from v1.4.x, please update your
federation-apiserver and federation-controller-manager manifests to the new version ([#30601](https://github.com/kubernetes/kubernetes/pull/30601), [@madhusudancs](https://github.com/madhusudancs))
- The deprecated kubelet --configure-cbr0 flag has been removed, and with that the "classic" networking mode as well. If you depend on this mode, please investigate whether the other network plugins
kubenet or cni meet your needs. ([#34906](https://github.com/kubernetes/kubernetes/pull/34906), [@luxas](https://github.com/luxas))
- New client-go structure, refer to kubernetes/client-go for versioning policy ([#34989](https://github.com/kubernetes/kubernetes/pull/34989), [@caesarxuchao](https://github.com/caesarxuchao))
- The deprecated kube-scheduler --bind-pods-qps and --bind-pods burst flags have been removed, use --kube-api-qps and --kube-api-burst instead ([#34471](https://github.com/kubernetes/kubernetes/pull/34471), [@timothysc](https://github.com/timothysc))
- If you used the PodDisruptionBudget feature in 1.4 (i.e. created
PodDisruptionBudget objects), then BEFORE upgrading from 1.4 to 1.5, you must delete all PodDisruptionBudget objects (policy/v1alpha1/PodDisruptionBudget) that you have created. It is not possible to delete these objects after you upgrade, and their presence will prevent you from using the beta PodDisruptionBudget feature in 1.5 (which uses policy/v1beta1/PodDisruptionBudget). If you have already upgraded, you will need to downgrade the master to 1.4 to delete the policy/v1alpha1/PodDisruptionBudget objects.
External Dependency Version Information
Continuous integration builds have used the following versions of external dependencies, however, this is not a strong recommendation and users should consult an appropriate installation or upgrade guide before deciding what versions of etcd, docker or rkt to use.
- Docker versions 1.10.3 - 1.12.3
- Docker version 1.11.2 known issues
- Docker version 1.12.1 has been validated through the Kubernetes docker automated validation framework as has Docker version 1.12.3
- Docker 1.10.3 contains backports provided by RedHat for known issues
- Docker versions as old as may 1.9.1 work with known issues but this is not guaranteed
- rkt version 1.21.0
- etcd version 2.2.1
Changelog since v1.5.0-beta.3
Other notable changes
Previous Releases Included in v1.5.0
v1.4.7
Documentation & Examples
Downloads for v1.4.7
| filename |
sha256 hash |
| kubernetes.tar.gz |
d193f76e70322010b3e86ac61c7a893175f9e62d37bece87cfd14ea068c8d187 |
| kubernetes-src.tar.gz |
7c7ef45e903ed2691c73bb2752805f190b4042ba233a6260f2cdeab7d0ac9bd3 |
Client Binaries
Server Binaries
Changelog since v1.4.6
Other notable changes
- Exit with error if is not the final parameter. (#37723, @mtaufen)
- Fix GCI mounter issue (#38124, @jingxu97)
- Fix space issue in volumePath with vSphere Cloud Provider (#38338, @BaluDontu)
- Fix panic in vSphere cloud provider (#38423, @BaluDontu)
- Changed default scsi controller type in vSphere Cloud Provider (#38426, @abrarshivani)
- Fix unmountDevice issue caused by shared mount in GCI (#38411, @jingxu97)
- Implement CanMount() for gfsMounter for linux (#36686, @rkouj)
- Better messaging for missing volume binaries on host (#36280, @rkouj)
- fix mesos unit tests (#38196, @deads2k)
- Fix Service Update on LoadBalancerSourceRanges Field (#37720, @freehan)
- Include serial port output in GCP log-dump (#37248, @mtaufen)
- Collect installation and configuration service logs for tests (#37401, @mtaufen)
- Use shasum if sha1sum doesn't exist in the path (#37362, @roberthbailey)
- Guard the ready replica checking by server version (#37303, @krousey)
- Fix issue when attempting to unmount a wrong vSphere volume (#37413, @BaluDontu)
- Fix issue in converting AWS volume ID from mount paths (#36840, @jingxu97)
- Correct env var name in configure-helper (#33848, @mtaufen)
- wait until the pods are deleted completely (#34778, @ymqytw)
- AWS: recognize us-east-2 region (#35013, @justinsb)
- Replace controller presence checking logic (#36924, @krousey)
- Fix a bug in scheduler happening after retrying unsuccessful bindings (#37293, @wojtek-t)
- Try self-repair scheduler cache or panic (#37379, @wojtek-t)
- Ignore mirror pods with RestartPolicy == Never in restart tests (#34462, @yujuhong)
- Change image-puller restart policy to OnFailure (#37070, @gmarek)
- Filter out non-RestartAlways mirror pod in restart test. (#37203, @Random-Liu)
- Validate volume spec before returning azure mounter (#37018, @rootfs)
- Networking test rewrite (#31559, @bprashanth)
- Fix the equality checks for numeric values in cluster/gce/util.sh. (#37638, @roberthbailey)
- Use gsed on the Mac (#37562, @roberthbailey)
- Fix TestServiceAlloc flakes (#37487, @wojtek-t)
- Change ScheduledJob POD name suffix from hash to Unix Epoch (#36883, @jakub-d)
- Add support for NFSv4 and GlusterFS in GCI base image (#37336, @jingxu97)
- Use generous limits in the resource usage tracking tests (#36623, @yujuhong)
v1.5.0-beta.3
Documentation & Examples
Downloads for v1.5.0-beta.3
| filename |
sha256 hash |
| kubernetes.tar.gz |
c2b29b38d29829b7b2591559d0d36495d463de0e18a2611bd1d66f2baea6352c |
| kubernetes-src.tar.gz |
0b3327b6f0b024c989aba1e546d50d56fc89ed6df74c09fc55b9f9c4a667b771 |
Client Binaries
Server Binaries
Changelog since v1.5.0-beta.2
Other notable changes
- Better compat with very old iptables (e.g. CentOS 6) (#37594, @thockin)
- fix permissions when using fsGroup (#37009, @sjenning)
- Fix GCI mounter issue (#38124, @jingxu97)
- fix mesos unit tests (#38196, @deads2k)
- Fix Service Update on LoadBalancerSourceRanges Field (#37720, @freehan)
- Fix Service Update on LoadBalancerSourceRanges Field (#37720, @freehan)
- Set kernel.softlockup_panic =1 based on the flag. (#38001, @dchen1107)
- Fix logic error in graceful deletion (#37721, @derekwaynecarr)
- Enable containerized mounter only for nfs and glusterfs types (#37990, @jingxu97)
- GCI: Remove /var/lib/docker/network (#37593, @yujuhong)
- kubelet: don't reject pods without adding them to the pod manager (#37661, @yujuhong)
- Fix photon controller plugin to construct with correct PdID (#37167, @luomiao)
- Fix the equality checks for numeric values in cluster/gce/util.sh. (#37638, @roberthbailey)
- federation service controller: stop deleting services from underlying clusters when federated service is deleted. (#37353, @nikhiljindal)
- Set Dashboard UI version to v1.5.0 (#37684, @rf232)
- When deleting an object with
--grace-period=0, the client will begin a graceful deletion and wait until the resource is fully deleted. To force deletion, use the --force flag. (#37263, @smarterclayton)
- Removes shorthand flag -w from kubectl apply (#37345, @MrHohn)
- Update doc for kubectl apply (#37397, @ymqytw)
- Try self-repair scheduler cache or panic (#37379, @wojtek-t)
- Use gsed on the Mac (#37562, @roberthbailey)
- Fix TestServiceAlloc flakes (#37487, @wojtek-t)
v1.5.0-beta.2
Documentation & Examples
Downloads for v1.5.0-beta.2
| filename |
sha256 hash |
| kubernetes.tar.gz |
4a6cb512dee2312ffe291f4209759309576ca477cf51fb8447b30a7cb2a887ed |
| kubernetes-src.tar.gz |
fe71f19b607183da4abf5f537e7ccbe72ac3306b0933ee1f519253c78bf9252f |
Client Binaries
Server Binaries
Changelog since v1.5.0-beta.1
Other notable changes
- Modify GCI mounter to enable NFSv3 (#36610, @jingxu97)
- Third party resources are now deleted when a namespace is deleted. (#35947, @brendandburns)
- kube-dns (#36775, @bowei)
- Added --config-map and --config-map-namespace command line options.
- If --config-map is set, kube-dns will load dynamic configuration from the config map
- referenced by --config-map-namespace, --config-map. The config-map supports
- the following properties: "federations".
- --federations flag is now deprecated. Prefer to set federations via the config-map.
- Federations can be configured by settings the "federations" field to the value currently
- set in the command line.
- Example:
- kind: ConfigMap
- apiVersion: v1
- metadata:
-
name: kube-dns
-
namespace: kube-system
- data:
-
federations: abc=def
- azure: support multiple ipconfigs on a NIC (#36841, @colemickens)
- Fix issue in converting AWS volume ID from mount paths (#36840, @jingxu97)
- fix leaking memory backed volumes of terminated pods (#36779, @sjenning)
- Default logging subsystem's resiliency was greatly improved, fluentd memory consumption and OOM error probability was reduced. (#37021, @Crassirostris)
v1.5.0-beta.1
Documentation & Examples
Downloads for v1.5.0-beta.1
| filename |
sha256 hash |
| kubernetes.tar.gz |
62c51bcee460794cda30e720c65509b679b51015c62c075e6e735fe29d089e2b |
| kubernetes-src.tar.gz |
8c950c7377eb40670d0438ccb68bbeaf1100ed2e919e012bc98479ff07ddd393 |
Client Binaries
Server Binaries
Changelog since v1.5.0-alpha.2
Action Required
Other notable changes
- Federation: allow specification of dns zone by ID (#36336, @justinsb)
- K8s 1.5 keeps container-vm as the default node image on GCE for backwards compatibility reasons. Please beware that container-vm is officially deprecated (supported with security patches only) and you should replace it with GCI if at all possible. You can review the migration guide here for more detail: https://cloud.google.com/container-engine/docs/node-image-migration (#36822, @mtaufen)
- Add a flag allowing contention profiling of the API server (#36756, @gmarek)
- Rename
--cgroups-per-qos to --experimental-cgroups-per-qos in Kubelet (#36767, @vishh)
- Implement CanMount() for gfsMounter for linux (#36686, @rkouj)
- Default host user namespace via experimental flag (#31169, @pweil-)
- Use generous limits in the resource usage tracking tests (#36623, @yujuhong)
- Update Dashboard UI version to 1.4.2 (#35895, @rf232)
- Add support for service load balancer source ranges to Azure load balancers. (#36696, @brendandburns)
- gci-dev-56-8977-0-0: (#36681, @mtaufen)
- Fix strategic patch for list of primitive type with merge sementic (#35647, @ymqytw)
- Fix issue in reconstruct volume data when kubelet restarts (#36616, @jingxu97)
- Ensure proper serialization of updates and creates in federation test watcher (#36613, @mwielgus)
- Add support for SourceIP preservation in Azure LBs (#36557, @brendandburns)
- Fix fetching pids running in a cgroup, which caused problems with OOM score adjustments & setting the /system cgroup ("misc" in the summary API). (#36551, @timstclair)
- federation: Adding support for DeleteOptions.OrphanDependents for federated replicasets and deployments. Setting it to false while deleting a federated replicaset or deployment also deletes the corresponding resource from all registered clusters. (#36476, @nikhiljindal)
- kubectl: show node label if defined (#35901, @justinsb)
- Migrates addons from RCs to Deployments (#36008, @MrHohn)
- Avoid setting S_ISGID on files in volumes (#36386, @sjenning)
- federation: Adding support for DeleteOptions.OrphanDependents for federated daemonsets and ingresses. Setting it to false while deleting a federated daemonset or ingress also deletes the corresponding resource from all registered clusters. (#36330, @nikhiljindal)
- Add authz to psp admission (#33080, @pweil-)
- Better messaging for missing volume binaries on host (#36280, @rkouj)
- Add Windows support to kube-proxy (#36079, @jbhurat)
- Support persistent volume usage for kubernetes running on Photon Controller platform (#36133, @luomiao)
- GCI nodes use an external mounter script to mount NFS & GlusterFS storage volumes (#36267, @vishh)
- Add retry to node scheduability marking. (#36211, @brendandburns)
- specify custom ca file to verify the keystone server (#35488, @dixudx)
- AWS: Support default value for ExternalHost (#33568, @justinsb)
- HPA: Consider unready pods separately (#33593, @DirectXMan12)
- Node Conformance Test: Containerize the node e2e test (#31093, @Random-Liu)
- federation: Adding support for DeleteOptions.OrphanDependents for federated secrets. Setting it to false while deleting a federated secret also deletes the corresponding secrets from all registered clusters. (#36296, @nikhiljindal)
- Deploy kube-dns with cluster-proportional-autoscaler (#33239, @MrHohn)
- Adds support for StatefulSets in kubectl drain. (#35483, @ymqytw)
- Switches to use the eviction sub-resource instead of deletion in kubectl drain, if server supports.
- azure: load balancer preserves destination ip address (#36256, @colemickens)
- LegacyHostIP will be deprecated in 1.7. (#36095, @caesarxuchao)
- Fix LBaaS version detection in openstack cloudprovider (#36249, @sjenning)
- Node Conformance Test: Add system verification (#32427, @Random-Liu)
- kubelet bootstrap: start hostNetwork pods before we have PodCIDR (#35526, @justinsb)
- Enable HPA controller based on autoscaling/v1 api group (#36215, @piosz)
- Remove unused WaitForDetach from Detacher interface and plugins (#35629, @kiall)
- Initial work on running windows containers on Kubernetes (#31707, @alexbrand)
- Per Volume Inode Accounting (#35132, @dashpole)
- [AppArmor] Hold bad AppArmor pods in pending rather than rejecting (#35342, @timstclair)
- Federation: separate notion of zone-name & dns-suffix (#35372, @justinsb)
- In order to bypass graceful deletion of pods (to immediately remove the pod from the API) the user must now provide the
--force flag in addition to --grace-period=0. This prevents users from accidentally force deleting pods without being aware of the consequences of force deletion. Force deleting pods for resources like StatefulSets can result in multiple pods with the same name having running processes in the cluster, which may lead to data corruption or data inconsistency when using shared storage or common API endpoints. (#35484, @smarterclayton)
- NPD: Add e2e test for NPD v0.2. (#35740, @Random-Liu)
- DELETE requests can now pass in their DeleteOptions as a query parameter or a body parameter, rather than just as a body parameter. (#35806, @bdbauer)
- make using service account credentials from controllers optional (#35970, @deads2k)
- AWS: strong-typing for k8s vs aws volume ids (#35883, @justinsb)
- Controller changes for perma failed deployments (#35691, @kargakis)
- Proxy min sync period (#35334, @timothysc)
- Federated ConfigMap controller (#35635, @mwielgus)
- have basic kubectl crud agnostic of registered types (#36085, @deads2k)
- Fix how we iterate over active jobs when removing them for Replace policy (#36161, @soltysh)
- Adds TCPCloseWaitTimeout option to kube-proxy for sysctl nf_conntrack_tcp_timeout_time_wait (#35919, @bowei)
- Pods that are terminating due to eviction by the nodecontroller (typically due to unresponsive kubelet, or network partition) now surface in
kubectl get output (#36017, @foxish)
- as being in state "Unknown", along with a longer description in
kubectl describe output.
- The hostname of the node (as autodetected by the kubelet, specified via --hostname-override, or determined by the cloudprovider) is now recorded as an address of type "Hostname" in the status of the Node API object. The hostname is expected to be resolveable from the apiserver. (#25532, @mkulke)
- [Kubelet] Add alpha support for
--cgroups-per-qos using the configured --cgroup-driver. Disabled by default. (#31546, @derekwaynecarr)
- Move Statefulset (previously PetSet) to v1beta1 (#35731, @janetkuo)
- The error handling behavior of
pkg/client/restclient.Result has changed. Calls to Result.Raw() will no longer parse the body, although they will still return errors that react to pkg/api/errors.Is*() as in previous releases. Callers of Get() and Into() will continue to receive errors that are parsed from the body if the kind and apiVersion of the body match the Status object. (#36001, @smarterclayton)
- This more closely aligns rest client as a generic RESTful client, while preserving the special Kube API extended error handling for the
Get and Into methods (which most Kube clients use).
- Making the pod.alpha.kubernetes.io/initialized annotation optional in PetSet pods (#35739, @foxish)
- AWS: recognize us-east-2 region (#35013, @justinsb)
- Eviction manager evicts based on inode consumption (#35137, @dashpole)
- SELinux Overhaul (#33663, @pmorie)
- Add SNI support to the apiserver (#35109, @sttts)
- The main kubernetes repository stops hosting archived version of released clients. Please use client-go. (#35928, @caesarxuchao)
- Correct the article in generated documents (#32557, @asalkeld)
- Update PodAntiAffinity to ignore calls to subresources (#35608, @soltysh)
- The apiserver can now select which type of kubelet-reported address to use for apiserver->node communications, using the --kubelet-preferred-address-types flag. (#35497, @liggitt)
- update list of vailable resources (#32687, @jouve)
- Remove stale volumes if endpoint/svc creation fails. (#35285, @humblec)
- add kubectl cp (#34914, @brendandburns)
- Remove Job also from .status.active for Replace strategy (#35420, @soltysh)
- Let release_1_5 clientset include multiple versions of a group (#35471, @caesarxuchao)
- support editing before creating resource (#33250, @ymqytw)
- allow authentication through a front-proxy (#35452, @deads2k)
- On GCI, cleanup kubelet startup (#35319, @vishh)
- Add a retry when reading a file content from a container (#35560, @jingxu97)
- Fix cadvisor_unsupported and the crossbuild (#35817, @luxas)
- [PHASE 1] Opaque integer resource accounting. (#31652, @ConnorDoyle)
- Add sync state loop in master's volume reconciler (#34859, @jingxu97)
- Bump GCE debian image to container-vm-v20161025 (CVE-2016-5195 Dirty… (#35825, @dchen1107)
- GC pod ips (#35572, @bprashanth)
- Stop including arch-specific binaries in kubernetes.tar.gz (#35737, @ixdy)
- Rename PetSet to StatefulSet (#35663, @janetkuo)
- Enable containerized storage plugins mounter on GCI (#35350, @vishh)
- Bump container-vm version in config-test.sh (#35705, @mtaufen)
- Cadvisor root path configuration (#35136, @dashpole)
- ssh pubkey parsing: prevent segfault (#35323, @mikkeloscar)
v1.4.6
Documentation & Examples
Downloads for v1.4.6
| filename |
sha256 hash |
| kubernetes.tar.gz |
6f8242aa29493e1f824997748419e4a287c28b06ed13f17b1ba94bf07fdfa3be |
| kubernetes-src.tar.gz |
a2a2d885d246300b52adb5d7e1471b382c77d90a816618518c2a6e9941208e40 |
Client Binaries
Server Binaries
Changelog since v1.4.5
Other notable changes
gci-beta-55-8872-47-0:
Date: Nov 11, 2016
Kernel: ChromiumOS-4.4
Kubernetes: v1.4.5
Docker: v1.11.2
Changelog (vs 55-8872-18-0)
* Cherry-pick runc PR#608: Eliminate redundant parsing of mountinfo
* Updated kubernetes to v1.4.5
* Fixed a bug in e2fsprogs that caused mke2fs to take a very long time. Upstream fix: http://git.kernel.org/cgit/fs/ext2/e2fsprogs.git/commit/?h=next&id=d33e690fe7a6cbeb51349d9f2c7fb16a6ebec9c2
- Fix fetching pids running in a cgroup, which caused problems with OOM score adjustments & setting the /system cgroup ("misc" in the summary API). (#36614, @timstclair)
- DELETE requests can now pass in their DeleteOptions as a query parameter or a body parameter, rather than just as a body parameter. (#35806, @bdbauer)
- rkt: Convert image name to be a valid acidentifier (#34375, @euank)
- Remove stale volumes if endpoint/svc creation fails. (#35285, @humblec)
- Remove Job also from .status.active for Replace strategy (#35420, @soltysh)
- Update PodAntiAffinity to ignore calls to subresources (#35608, @soltysh)
- Adds TCPCloseWaitTimeout option to kube-proxy for sysctl nf_conntrack_tcp_timeout_time_wait (#35919, @bowei)
- Fix how we iterate over active jobs when removing them for Replace policy (#36161, @soltysh)
- Bump GCI version to latest m55 version in GCE for K8s 1.4 (#36302, @mtaufen)
- Add a check for file size if the reading content returns empty (#33976, @jingxu97)
- Add a retry when reading a file content from a container (#35560, @jingxu97)
- Skip CLOSE_WAIT e2e test if server is 1.4.5 (#36404, @bowei)
- Adds etcd3 changes (#36232, @wojtek-t)
- Adds TCPCloseWaitTimeout option to kube-proxy for sysctl nf_conntrack_tcp_timeout_time_wait (#36099, @bowei)
v1.3.10
Documentation & Examples
Downloads for v1.3.10
| filename |
sha256 hash |
| kubernetes.tar.gz |
0f61517fbab1feafbe1024da0b88bfe16e61fed7e612285d70e3ecb53ce518cf |
| kubernetes-src.tar.gz |
7b1be0dcc12ae1b0cb1928b770c1025755fd0858ce7520907bacda19e5bfa53f |
Client Binaries
Server Binaries
Changelog since v1.3.9
Other notable changes
- gci: decouple from the built-in kubelet version (#31367, @Amey-D)
- Bump GCE debian image to container-vm-v20161025 (CVE-2016-5195 Dirty… (#35825, @dchen1107)
- Add RELEASE_INFRA_PUSH related code to support pushes from kubernetes/release. (#28922, @david-mcmahon)
v1.4.5
Documentation & Examples
Downloads for v1.4.5
| filename |
sha256 hash |
| kubernetes.tar.gz |
339f4d1c7a374ddb32334268c4af8dae0b86d1567a9c812087d672a7defe233c |
| kubernetes-src.tar.gz |
69b1b022400794d491200a9365ea9bf735567348d0299920462cf7167c76ba61 |
Client Binaries
Server Binaries
Changelog since v1.4.4
Other notable changes
- Fix volume states out of sync problem after kubelet restarts (#33616, @jingxu97)
- cross: add IsNotMountPoint() to mount_unsupported.go (#35566, @rootfs)
- Bump GCE debian image to container-vm-v20161025 (CVE-2016-5195 Dirty COW) (#35825, @dchen1107)
- Avoid overriding system and kubelet cgroups on GCI (#35319, @vishh)
* Make the kubectl from k8s release the default on GCI
- kubelet summary rootfs now refers to the filesystem that contains the Kubelet RootDirectory (var/lib/kubelet) instead of cadvisor's rootfs ( / ), since they may be different filesystems. (#35136, @dashpole)
- Fix cadvisor_unsupported and the crossbuild (#35817, @luxas)
- kubenet: SyncHostports for both running and ready to run pods. (#31388, @yifan-gu)
- GC pod ips (#35572, @bprashanth)
- Fix version string generation for local version different from release and not based on
-alpha.no or -beta.no suffixed tag. (#34612, @jellonek)
- Node status updater should SetNodeStatusUpdateNeeded if it fails to update status (#34368, @jingxu97)
- Fixed flakes caused by petset tests. (#35158, @foxish)
- Added rkt binary to GCI (#35321, @vishh)
- Bump container-vm version in config-test.sh (#35705, @mtaufen)
- Delete all firewall rules (and optionally network) on GCE/GKE cluster teardown (#34577, @ixdy)
- Fixed mutation warning in Attach/Detach controller (#35273, @jsafrane)
- Dynamic provisioning for vSphere (#30836, @abrarshivani)
- Update grafana version used by default in kubernetes to 3.1.1 (#35435, @Crassirostris)
- vSphere Kube-up: resolve vm-names on all nodes (#35365, @kerneltime)
- Improve source IP preservation test, fail the test instead of panic. (#34030, @MrHohn)
- Fix #31085, include output checking in retry loop (#34107, @MrHohn)
- vSphere kube-up: Wait for cbr0 configuration to complete before setting up routes. (#35232, @kerneltime)
- Substitute gcloud regex with regexp (#35346, @bprashanth)
- Fix PDB e2e test, off-by-one (#35274, @soltysh)
- etcd3: API storage - decouple decorator from filter (#31189, @hongchaodeng)
- etcd3: v3client + grpc client leak fix (#31704, @timothysc)
- etcd3: watcher logging error (#32831, @hongchaodeng)
- etcd: watcher centralize error handling (#32907, @hongchaodeng)
- etcd: stop watcher when watch channel is closed (#33003, @hongchaodeng)
- etcd3: dereference the UID pointer for a readable error message. (#33349, @madhusudancs)
- etcd3: pass SelectionPredicate instead of Filter to storage layer (#31190, @hongchaodeng)
- etcd3: make gets for previous value in watch serialize-able (#34089, @wojtek-t)
- etcd3: minor cleanups (#34234, @wojtek-t)
- etcd3: update etcd godep to 3.0.9 to address TestWatch issues (#32822, @timothysc)
- etcd3: update to etcd 3.0.10 (#33393, @timothysc)
- etcd3: use PrevKV to remove additional get (#34246, @hongchaodeng)
- etcd3: avoid unnecessary decoding in etcd3 client (#34435, @wojtek-t)
- etcd3: fix suite (#32477, @wojtek-t)
v1.5.0-alpha.2
Documentation & Examples
Downloads for v1.5.0-alpha.2
| filename |
sha256 hash |
| kubernetes.tar.gz |
77f04c646657b683210a17aeca62e56bf985702b267942b41729406970c40cee |
| kubernetes-src.tar.gz |
f6090cc853e56159099bf12169f0d84e29fd2c055b0c7dbdac755ee94439a6a6 |
Client Binaries
Server Binaries
Changelog since v1.5.0-alpha.1
Action Required
- Deprecate the --reconcile-cidr kubelet flag because it has no function anymore (#35523, @luxas)
- Removed the deprecated kubelet --configure-cbr0 flag, and with that the "classic" networking mode as well (#34906, @luxas)
- New client-go structure (#34989, @caesarxuchao)
- Remove scheduler flags that were marked as deprecated 2+ releases ago. (#34471, @timothysc)
Other notable changes
- Make the fake RESTClient usable by all the API groups, not just core. (#35492, @madhusudancs)
- Adding support for DeleteOptions.OrphanDependents for federated namespaces. Setting it to false while deleting a federated namespace also deletes the corresponding namespace from all registered clusters. (#34648, @nikhiljindal)
- Kubelet flag '--mounter-path' renamed to '--experimental-mounter-path' (#35646, @vishh)
- Node status updater should SetNodeStatusUpdateNeeded if it fails to update status (#34368, @jingxu97)
- Deprecate OpenAPI spec for GroupVersion endpoints in favor of single spec /swagger.json (#35388, @mbohlool)
- kubelet authn/authz (#34381, @liggitt)
- Fix volume states out of sync problem after kubelet restarts (#33616, @jingxu97)
- Added rkt binary to GCI (#35321, @vishh)
- Fixed mutation warning in Attach/Detach controller (#35273, @jsafrane)
- Don't count failed pods as "not-ready" (#35404, @brendandburns)
- fixed typo in script which made setting custom cidr in gce using kube-up impossible (#35267, @tommywo)
- The podGC controller will now always run, irrespective of the value supplied to the "terminated-pod-gc-threshold" flag supplied to the controller manager. (#35476, @foxish)
- The specific behavior of the podGC controller to clean up terminated pods is still governed by the flag, but the podGC's responsibilities have evolved beyond just cleaning up terminated pods.
- Update grafana version used by default in kubernetes to 3.1.1 (#35435, @Crassirostris)
- vSphere Kube-up: resolve vm-names on all nodes (#35365, @kerneltime)
- bootstrap: Start hostNetwork pods even if network plugin not ready (#33347, @justinsb)
- Factor out post-init swagger and OpenAPI routes (#32590, @sttts)
- Substitute gcloud regex with regexp (#35346, @bprashanth)
- Remove support for multi-architecture code in
kubeadm, which was released untested. (#35124, @errordeveloper)
- vSphere kube-up: Wait for cbr0 configuration to complete before setting up routes. (#35232, @kerneltime)
- Remove last probe time from replica sets (#35199, @kargakis)
- Update the GCI image to gci-dev-55-8872-18-0 (#35243, @maisem)
- Add
--mounter-path flag to kubelet that will allow overriding the mount command used by kubelet (#34994, @jingxu97)
- Fix a bug under the rkt runtime whereby image-registries with ports would not be fetched from (#34375, @euank)
- Updated default Elasticsearch and Kibana used for elasticsearch logging destination to versions 2.4.1 and 4.6.1 respectively. (#34969, @Crassirostris)
- Loadbalanced client src ip preservation enters beta (#33957, @bprashanth)
- Add NodePort value in kubectl output (#34922, @zreigz)
- kubectl drain now waits until pods have been delete from the Node before exiting (#34778, @ymqytw)
- Don't report FS stats for system containers in the Kubelet Summary API (#34998, @timstclair)
- Fixed flakes caused by petset tests. (#35158, @foxish)
- Add validation that detects repeated keys in the labels and annotations maps (#34407, @brendandburns)
- Change merge key for VolumeMount to mountPath (#35071, @thockin)
- kubelet: storage: don't hang kubelet on unresponsive nfs (#35038, @sjenning)
- Fix kube vsphere.kerneltime (#34997, @kerneltime)
- Add PSP support for seccomp profiles (#28300, @pweil-)
- Updated Go to 1.7 (#28742, @jessfraz)
- HPA: fixed wrong count for target replicas calculations (#34821). (#34955, @jszczepkowski)
- Improves how 'kubectl' uses the terminal size when printing help and usage. (#34502, @fabianofranz)
- Updated Elasticsearch image from version 1.5.1 to version 2.4.1. Updated Kibana image from version 4.0.2 to version 4.6.1. (#34562, @Crassirostris)
- libvirt-coreos: Download the coreos_production_qemu_image over SSL. (#34646, @roberthbailey)
- Add a new global option "--request-timeout" to the
kubectl client (#33958, @juanvallejo)
- Add support for admission controller based on namespace node selectors. (#24980, @aveshagarwal)
- Add 'kubectl set resources' (#27206, @JacobTanenbaum)
- Support trust id as a scope in the OpenStack authentication logic (#32111, @MatMaul)
- Only wait for cache syncs once in NodeController (#34851, @ncdc)
- NodeController waits for informer sync before doing anything (#34809, @gmarek)
- azure: lower log priority for skipped nic update message (#34730, @colemickens)
- Security Group support for OpenStack Load Balancers (#31921, @grahamhayes)
- Make NodeController recognize deletion tombstones (#34786, @davidopp)
- Delete all firewall rules (and optionally network) on GCE/GKE cluster teardown (#34577, @ixdy)
- Fix panic in NodeController caused by receiving DeletedFinalStateUnknown object from the cache. (#34694, @gmarek)
- azure: add PrimaryAvailabilitySet to config, only use nodes in that set in the loadbalancer pool (#34526, @colemickens)
- Fix leaking ingress resources in federated ingress e2e test. (#34652, @quinton-hoole)
- pvc.Spec.Resources.Requests min and max can be enforced with a LimitRange of type "PersistentVolumeClaim" in the namespace (#30145, @markturansky)
- Federated DaemonSet controller. Supports all the API that regular DaemonSet has. (#34319, @mwielgus)
- New federation deployment mechanism now allows non-GCP clusters. (#34620, @madhusudancs)
* Writes the federation kubeconfig to the local kubeconfig file.
- Update the series and the README to reflect the change. (#30374, @mbruzek)
- Replica set conditions API (#33905, @kargakis)
- etcd3: avoid unnecessary decoding in etcd3 client (#34435, @wojtek-t)
- Test x509 intermediates correctly (#34524, @liggitt)
- Add
cifs-utils to the hyperkube image. (#34416, @colemickens)
- etcd3: use PrevKV to remove additional get (#34246, @hongchaodeng)
- Fix upgrade.sh image setup (#34468, @mtaufen)
v1.2.7
Documentation & Examples
Downloads for v1.2.7
| filename |
sha256 hash |
| kubernetes.tar.gz |
53db157923c17fa7a0addb3e4dfe7d1b9194b9266a87d371a251d5bb790a1832 |
| kubernetes-src.tar.gz |
e6e46831706743d8263581d0575507cf5ffc265096d22e5e84cf1c3ae925db5e |
Client Binaries
Server Binaries
Changelog since v1.2.6
Other notable changes
v1.4.4
Documentation & Examples
Downloads for v1.4.4
| filename |
sha256 hash |
| kubernetes.tar.gz |
2732bfc56ceabc872b6af3f460cbda68c2384c95a1c0c72eb33e5ff0e03dc9da |
| kubernetes-src.tar.gz |
29c6cf1567e6b7f6c3ecb71acead083b7535b22ac20bd8166b29074e8a0f6441 |
Client Binaries
Server Binaries
Changelog since v1.4.3
Other notable changes
- Update the GCI image to gci-dev-55-8872-18-0 (#35243, @maisem)
- Change merge key for VolumeMount to mountPath (#35071, @thockin)
- Turned-off etcd listening on public ports as potentially insecure. Removed (#35192, @jszczepkowski)
- experimental support for master replication.
- Add support for vSphere Cloud Provider when deploying via kubeup on vSphere. (#31467, @kerneltime)
- Fix kube vsphere.kerneltime (#34997, @kerneltime)
- HPA: fixed wrong count for target replicas calculations (#34821). (#34955, @jszczepkowski)
- Fix leaking ingress resources in federated ingress e2e test. (#34652, @quinton-hoole)
- azure: add PrimaryAvailabilitySet to config, only use nodes in that set in the loadbalancer pool (#34526, @colemickens)
- azure: lower log priority for skipped nic update message (#34730, @colemickens)
v1.3.9
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
a994c732d2b852bbee55a78601d50d046323021a99b0801aea07dacf64c2c59a |
Changelog since v1.3.8
Other notable changes
v1.4.3
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
c3dccccc005bc22eaf814ccb8e72b4f876167ab38ac594bb7e44c98f162a0f1c |
Changelog since v1.4.2-beta.1
Other notable changes
- Fix non-starting node controller in 1.4 branch (#34895, @wojtek-t)
- Cherrypick #34851 "Only wait for cache syncs once in NodeController" (#34861, @jessfraz)
- NodeController waits for informer sync before doing anything (#34809, @gmarek)
- Make NodeController recognize deletion tombstones (#34786, @davidopp)
- Fix panic in NodeController caused by receiving DeletedFinalStateUnknown object from the cache. (#34694, @gmarek)
- Update GlusterFS provisioning readme with endpoint/service details (#31854, @humblec)
- Add logging for enabled/disabled API Groups (#32198, @deads2k)
- New federation deployment mechanism now allows non-GCP clusters. (#34620, @madhusudancs)
* Writes the federation kubeconfig to the local kubeconfig file.
v1.4.2
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
0730e207944ca96c9d9588a571a5eff0f8fdbb0e1287423513a2b2a4baca9f77 |
Changelog since v1.4.2-beta.1
Other notable changes
- Cherrypick #34851 "Only wait for cache syncs once in NodeController" (#34861, @jessfraz)
- NodeController waits for informer sync before doing anything (#34809, @gmarek)
- Make NodeController recognize deletion tombstones (#34786, @davidopp)
- Fix panic in NodeController caused by receiving DeletedFinalStateUnknown object from the cache. (#34694, @gmarek)
- Update GlusterFS provisioning readme with endpoint/service details (#31854, @humblec)
- Add logging for enabled/disabled API Groups (#32198, @deads2k)
- New federation deployment mechanism now allows non-GCP clusters. (#34620, @madhusudancs)
* Writes the federation kubeconfig to the local kubeconfig file.
v1.5.0-alpha.1
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
86bfcfffaa210ddf18983ff066470ef9c06ee00449b2238043e2777aac2c906d |
Changelog since v1.4.0-alpha.3
Experimental Features
Action Required
- kube-apiserver learned the '--anonymous-auth' flag, which defaults to true. When enabled, requests to the secure port that are not rejected by other configured authentication methods are treated as anonymous requests, and given a username of 'system:anonymous' and a group of 'system:unauthenticated'. (#32386, @liggitt)
- Authenticated users are decorated with a 'system:authenticated' group.
- NOTE: anonymous access is enabled by default. If you rely on authentication alone to authorize access, change to use an authorization mode other than AlwaysAllow, or or set '--anonymous-auth=false'.
- The NamespaceExists and NamespaceAutoProvision admission controllers have been removed. (#31250, @derekwaynecarr)
- All cluster operators should use NamespaceLifecycle.
- Federation binaries and their corresponding docker images -
federation-apiserver and federation-controller-manager are now folded in to the hyperkube binary. If you were using one of these binaries or docker images, please switch to using the hyperkube version. Please refer to the federation manifests - federation/manifests/federation-apiserver.yaml and federation/manifests/federation-controller-manager-deployment.yaml for examples. (#29929, @madhusudancs)
Other notable changes
- The kube-apiserver --service-account-key-file option can be specified multiple times, or can point to a file containing multiple keys, to enable rotation of signing keys. (#34029, @liggitt)
- The apiserver now uses addresses reported by the kubelet in the Node object's status for apiserver->kubelet communications, rather than the name of the Node object. The address type used defaults to
InternalIP, ExternalIP, and LegacyHostIP address types, in that order. (#33718, @justinsb)
- Federated deployment controller that supports the same api as the regular kubernetes deployment controller. (#34109, @mwielgus)
- Match GroupVersionKind against specific version (#34010, @soltysh)
- fix yaml decode issue (#34297, @AdoHe)
- kubectl annotate now supports --dry-run (#34199, @asalkeld)
- kubectl: Add external ip information to node when '-o wide' is used (#33552, @floreks)
- Update GCI base image: (#34156, @adityakali)
* Enabled VXLAN and IP_SET config options in kernel to support some networking tools (ebtools)
* OpenSSL CVE fixes
- ContainerVm/GCI image: try to use ifdown/ifup if available (#33595, @freehan)
- Use manifest digest (as
docker-pullable://) as ImageID when available (exposes a canonical, pullable image ID for containers). (#33014, @DirectXMan12)
- Add kubelet awareness to taint tolerant match caculator. (#26501, @resouer)
- Fix nil pointer issue when getting metrics from volume mounter (#34251, @jingxu97)
- Enforce Disk based pod eviction with GCI base image in Kubelet (#33520, @vishh)
- Remove headers that are unnecessary for proxy target (#34076, @mbohlool)
- Add missing argument to log message in federated ingress controller. (#34158, @quinton-hoole)
- The kubelet --eviction-minimum-reclaim option can now take precentages as well as absolute values for resources quantities (#33392, @sjenning)
- The implicit registration of Prometheus metrics for workqueue has been removed, and a plug-able interface was added. If you were using workqueue in your own binaries and want these metrics, add the following to your imports in the main package: "k8s.io/pkg/util/workqueue/prometheus". (#33792, @caesarxuchao)
- Add kubectl --node-port option for specifying the service nodeport (#33319, @juanvallejo)
- To reduce memory usage to reasonable levels in smaller clusters, kube-apiserver now sets the deserialization cache size based on the target memory usage. (#34000, @wojtek-t)
- use service accounts as clients for controllers (#33310, @deads2k)
- Add a new option "--local" to the
kubectl annotate (#34074, @asalkeld)
- Add a new option "--local" to the
kubectl label (#33990, @asalkeld)
- Initialize podsWithAffinity to avoid scheduler panic (#33967, @xiang90)
- Fix base image pinning during upgrades via cluster/gce/upgrade.sh (#33147, @vishh)
- Remove the flannel experimental overlay (#33862, @luxas)
- CRI: Remove the mount name and port name. (#33970, @yifan-gu)
- Enable kubectl describe rs to work when apiserver does not support pods (#33794, @nikhiljindal)
- Heal the namespaceless ingresses in federation e2e. (#33977, @quinton-hoole)
- Fix issue in updating device path when volume is attached multiple times (#33796, @jingxu97)
- ECDSA keys can now be used for signing and verifying service account tokens. (#33565, @liggitt)
- OnlyLocal nodeports (#33587, @bprashanth)
- Remove flannel because now everything here is upstreamed (#33860, @luxas)
- Use patched golang1.7.1 for cross-builds targeting darwin (#33803, @ixdy)
- Bump up addon kube-dns to v20 for graceful termination (#33774, @MrHohn)
- Creating LoadBalancer Service with "None" ClusterIP is no longer possible (#33274, @nebril)
- Increase timeout for federated ingress test. (#33610, @quinton-hoole)
- Use UpdateStatus, not Update, to add LoadBalancerStatus to Federated Ingress. (#33605, @quinton-hoole)
- add anytoken authenticator (#33378, @deads2k)
- Fixes in HPA: consider only running pods; proper denominator in avg request calculations. (#33735, @jszczepkowski)
- When CORS Handler is enabled, we now add a new HTTP header named "Access-Control-Expose-Headers" with a value of "Date". This allows the "Date" HTTP header to be accessed from XHR/JavaScript. (#33242, @dims)
- promote contrib/mesos to incubator (#33658, @deads2k)
- MinReadySeconds / AvailableReplicas for ReplicaSets (#32771, @kargakis)
- Kubectl drain will now drain finished Pods (#31763, @fraenkel)
- Adds the -deployment option to e2e.go, adds the ability to run e2e.go using a
kops deployment. (#33518, @zmerlynn)
- Tune down initialDelaySeconds for readinessProbe. (#33146, @MrHohn)
- kube-proxy: Add a lower-bound for conntrack (128k default) (#33051, @thockin)
- local-up-cluster.sh: add SERVICE_CLUSTER_IP_RANGE as option (#32921, @aanm)
- Default HTTP2 on, post fixes from #29001 (#32231, @timothysc)
- Split dns healthcheck into two different urls (#32406, @MrHohn)
- Remove kubectl namespace command (#33275, @maciaszczykm)
- Automatic generation of man pages (#33277, @mkumatag)
- Fixes memory/goroutine leak in Federation Service controller. (#33359, @shashidharatd)
- Switch k8s on GCE to use GCI by default (#33353, @vishh)
- Move HighWaterMark to the top of the struct in order to fix arm, second time (#33376, @luxas)
- Fix race condition in setting node statusUpdateNeeded flag (#32807, @jingxu97)
- Fix the DOCKER_OPTS appending bug. (#33163, @DjangoPeng)
- Send recycle events from pod to pv. (#27714, @jsafrane)
- Add port forwarding for rkt with kvm stage1 (#32126, @jjlakis)
- The value of the
versioned.Event object (returned by watch APIs) in the Swagger 1.2 schemas has been updated from *versioned.Event which was not expected by many client tools. The new value is consistent with other structs returned by the API. (#33007, @smarterclayton)
- Remove cpu limits for dns pod to avoid CPU starvation (#33227, @vishh)
- Allow secure access to apiserver from Admission Controllers (#31491, @dims)
- Resolves x509 verification issue with masters dialing nodes when started with --kubelet-certificate-authority (#33141, @liggitt)
- Fix possible panic in PodAffinityChecker (#33086, @ivan4th)
- Upgrading Container-VM base image for k8s on GCE. Brief changelog as follows: (#32738, @Amey-D)
-
- Fixed performance regression in veth device driver
-
- Docker and related binaries are statically linked
-
- Fixed the issue of systemd being oom-killable
- Move HighWaterMark to the top of the struct in order to fix arm (#33117, @luxas)
- kubenet: SyncHostports for both running and ready to run pods. (#31388, @yifan-gu)
- Limit the number of names per image reported in the node status (#32914, @yujuhong)
- Support Quobyte as StorageClass (#31434, @johscheuer)
- Use a patched go1.7.1 for building linux/arm (#32517, @luxas)
- Add line break after events in kubectl describe (#31463, @fabianofranz)
- Specific error message on failed rolling update issued by older kubectl against 1.4 master (#32751, @caesarxuchao)
- Make the informer library available for the go client library. (#32718, @mikedanese)
- Added --log-facility flag to enhance dnsmasq logging (#32422, @MrHohn)
- Set Dashboard UI to final 1.4 version (#32666, @bryk)
- Fix audit_test regex for iso8601 timestamps (#32593, @johnbieren)
- Docker digest validation is too strict (#32627, @smarterclayton)
- Bumped Heapster to v1.2.0. (#32649, @piosz)
- add local subject access review API (#32407, @deads2k)
- make --runtime-config=api/all=true|false work (#32582, @jlowdermilk)
- Added new kubelet flags
--cni-bin-dir and --cni-conf-dir to specify where CNI files are located. (#32151, @bboreham)
- Fixed CNI configuration on GCI platform when using CNI.
- Move push-ci-build.sh to kubernetes/release repo (#32444, @david-mcmahon)
- vendor: update github.com/coreos/go-oidc client package (#31564, @ericchiang)
- Fixed an issue that caused a credential error when deploying federation control plane onto a GKE cluster. (#31747, @madhusudancs)
- NONE (#32229, @errordeveloper)
- Error if a contextName is provided but not found in the kubeconfig. (#31767, @asalkeld)
- Use a Deployment for kube-dns (#32018, @MrHohn)
- NONE (#32067, @erikh)
- Support graceful termination in kube-dns (#31894, @MrHohn)
- When prompting for passwords, don't echo to the terminal (#31586, @brendandburns)
- add group prefix matching for kubectl usage (#32140, @deads2k)
- Stick to 2.2.1 etcd (#32404, @caesarxuchao)
- Fix a bug in kubelet hostport logic which flushes KUBE-MARK-MASQ iptables chain (#32413, @freehan)
- Make sure finalizers prevent deletion on storage that supports graceful deletion (#32351, @caesarxuchao)
- AWS: Change default networking for kube-up to kubenet (#32239, @zmerlynn)
- Use etcd 2.3.7 (#32359, @wojtek-t)
- Allow missing keys in jsonpath (#31714, @smarterclayton)
- Changes 'kubectl rollout status' to wait until all updated replicas are available before finishing. (#31499, @areed)
- add selfsubjectaccessreview API (#31271, @deads2k)
- Add kubectl describe cmd support for vSphere volume (#31045, @abrarshivani)
- Enable kubelet eviction whenever inodes free is < 5% on GCE (#31545, @vishh)
- Use federated namespace instead of the bootstrap cluster's namespace in Ingress e2e tests. (#32105, @madhusudancs)
- Move StorageClass to a storage group (#31886, @deads2k)
- Some components like kube-dns and kube-proxy could fail to load the service account token when started within a pod. Properly handle empty configurations to try loading the service account config. (#31947, @smarterclayton)
- Removed comments in json config when using kubectl edit with -o json (#31685, @jellonek)
- fixes invalid null selector issue in sysdig example yaml (#31393, @baldwinSPC)
- Rescheduler which ensures that critical pods are always scheduled enabled by default in GCE. (#31974, @piosz)
- retry oauth token fetch in gce cloudprovider (#32021, @mikedanese)
- Deprecate the old cbr0 and flannel networking modes (#31197, @freehan)
- AWS: fix volume device assignment race condition (#31090, @justinsb)
- The certificates API group has been renamed to certificates.k8s.io (#31887, @liggitt)
- Increase Dashboard UI version to v1.4.0-beta2 (#31518, @bryk)
- Fixed incomplete kubectl bash completion. (#31333, @xingzhou)
- Added liveness probe to Heapster service. (#31878, @mksalawa)
- Adding clusters to the list of valid resources printed by kubectl help (#31719, @nikhiljindal)
- Kubernetes server components using
kubeconfig files no longer default to http://localhost:8080. Administrators must specify a server value in their kubeconfig files. (#30808, @smarterclayton)
- Update influxdb to 0.12 (#31519, @piosz)
- Include security options in the container created event (#31557, @timstclair)
- Federation can now be deployed using the
federation/deploy/deploy.sh script. This script does not depend on any of the development environment shell library/scripts. This is an alternative to the current federation-up.sh/federation-down.sh scripts. Both the scripts are going to co-exist in this release, but the federation-up.sh/federation-down.sh scripts might be removed in a future release in favor of federation/deploy/deploy.sh script. (#30744, @madhusudancs)
- Add get/delete cluster, delete context to kubectl config (#29821, @alexbrand)
- rkt: Force
rkt fetch to fetch from remote to conform the image pull policy. (#31378, @yifan-gu)
- Allow services which use same port, different protocol to use the same nodePort for both (#30253, @AdoHe)
- Handle overlapping deployments gracefully (#30730, @janetkuo)
- Remove environment variables and internal Kubernetes Docker labels from cAdvisor Prometheus metric labels. (#31064, @grobie)
- Old behavior:
-
- environment variables explicitly whitelisted via --docker-env-metadata-whitelist were exported as
container_env_*=*. Default is zero so by default non were exported
-
- all docker labels were exported as
container_label_*=*
- New behavior:
-
- Only
container_name, pod_name, namespace, id, image, and name labels are exposed
-
- no environment variables will be exposed ever via /metrics, even if whitelisted
- Filter duplicate network packets in promiscuous bridge mode (with ebtables) (#28717, @freehan)
- Refactor to simplify the hard-traveled path of the KubeletConfiguration object (#29216, @mtaufen)
- Fix overflow issue in controller-manager rate limiter (#31396, @foxish)
v1.4.2-beta.1
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
b72986a0adcb7e08feb580c5d72de129ac2ecc128c154fd79785bac2d2e760f7 |
Changelog since v1.4.1
Other notable changes
v1.4.1
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
b51971d872426ba71bb09b9a9191bb95fc0e48390dc287a9080e3876c8e19a95 |
Changelog since v1.4.1-beta.2
No notable changes for this release
v1.4.1-beta.2
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
708fbaabf17a69c69c2c9a715e152a29d47334b8c98d217ba17e9b42d6770f25 |
Changelog since v1.4.0
Other notable changes
- Update GCI base image: (#34156, @adityakali)
* Enabled VXLAN and IP_SET config options in kernel to support some networking tools (ebtools)
* OpenSSL CVE fixes
- ContainerVm/GCI image: try to use ifdown/ifup if available (#33595, @freehan)
- Make the informer library available for the go client library. (#32718, @mikedanese)
- Enforce Disk based pod eviction with GCI base image in Kubelet (#33520, @vishh)
- Fix nil pointer issue when getting metrics from volume mounter (#34251, @jingxu97)
- Enable kubectl describe rs to work when apiserver does not support pods (#33794, @nikhiljindal)
- Increase timeout for federated ingress test. (#33610, @quinton-hoole)
- Remove headers that are unnecessary for proxy target (#34076, @mbohlool)
- Support graceful termination in kube-dns (#31894, @MrHohn)
- Added --log-facility flag to enhance dnsmasq logging (#32422, @MrHohn)
- Split dns healthcheck into two different urls (#32406, @MrHohn)
- Tune down initialDelaySeconds for readinessProbe. (#33146, @MrHohn)
- Bump up addon kube-dns to v20 for graceful termination (#33774, @MrHohn)
- Send recycle events from pod to pv. (#27714, @jsafrane)
- Limit the number of names per image reported in the node status (#32914, @yujuhong)
- Fixes in HPA: consider only running pods; proper denominator in avg request calculations. (#33735, @jszczepkowski)
- Fix audit_test regex for iso8601 timestamps (#32593, @johnbieren)
- Limit the number of names per image reported in the node status (#32914, @yujuhong)
- Fix the DOCKER_OPTS appending bug. (#33163, @DjangoPeng)
- Remove cpu limits for dns pod to avoid CPU starvation (#33227, @vishh)
- Fixes memory/goroutine leak in Federation Service controller. (#33359, @shashidharatd)
- Use UpdateStatus, not Update, to add LoadBalancerStatus to Federated Ingress. (#33605, @quinton-hoole)
- Initialize podsWithAffinity to avoid scheduler panic (#33967, @xiang90)
- Heal the namespaceless ingresses in federation e2e. (#33977, @quinton-hoole)
- Add missing argument to log message in federated ingress controller. (#34158, @quinton-hoole)
- Fix issue in updating device path when volume is attached multiple times (#33796, @jingxu97)
- To reduce memory usage to reasonable levels in smaller clusters, kube-apiserver now sets the deserialization cache size based on the target memory usage. (#34000, @wojtek-t)
- Fix possible panic in PodAffinityChecker (#33086, @ivan4th)
- Fix race condition in setting node statusUpdateNeeded flag (#32807, @jingxu97)
- kube-proxy: Add a lower-bound for conntrack (128k default) (#33051, @thockin)
- Use patched golang1.7.1 for cross-builds targeting darwin (#33803, @ixdy)
- Move HighWaterMark to the top of the struct in order to fix arm (#33117, @luxas)
- Move HighWaterMark to the top of the struct in order to fix arm, second time (#33376, @luxas)
v1.3.8
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
66cf72d8f07e2f700acfcb11536694e0d904483611ff154f34a8380c63720a8d |
Changelog since v1.3.7
Other notable changes
v1.4.0
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
6cf3d78230f7659b87fa399a56a7aaed1fde6a73be9d05e25feedacfbd8d5a16 |
Major Themes
- Simplified User Experience
- Easier to get a cluster up and running (eg:
kubeadm, intra-cluster bootstrapping)
- Easier to understand a cluster (eg: API audit logs, server-based API defaults)
- Stateful Appplication Support
- Enhanced persistence capabilities (eg:
StorageClasses, new volume plugins)
- New resources and scheduler features (eg:
ScheduledJob resource, pod/node affinity/anti-affinity)
- Cluster Federation
- Global Multi-cluster HTTP(S) Ingress across GCE and GKE clusters.
- Expanded support for federated hybrid-cloud resources including ReplicaSets, Secrets, Namespaces and Events.
- Security
- Increased pod-level security granularity (eg: Container Image Policies, AppArmor and
sysctl support)
- Increased cluster-level security granularity (eg: Access Review API)
Features
This is the first release tracked via the use of the kubernetes/features issues repo. Each Feature issue is owned by a Special Interest Group from kubernetes/community
- API Machinery
- [alpha] Generate audit logs for every request user performs against secured API server endpoint. (docs) (kubernetes/features#22)
- [beta]
kube-apiserver now publishes a swagger 2.0 spec in addition to a swagger 1.2 spec (kubernetes/features#53)
- [beta] Server-side garbage collection is enabled by default. See user-guide
- Apps
- [alpha] Introducing 'ScheduledJobs', which allow running time based Jobs, namely once at a specified time or repeatedly at specified point in time. (docs) (kubernetes/features#19)
- Auth
- [alpha] Container Image Policy allows an access controller to determine whether a pod may be scheduled based on a policy (docs) (kubernetes/features#59)
- [alpha] Access Review APIs expose authorization engine to external inquiries for delegation, inspection, and debugging (docs) (kubernetes/features#37)
- Cluster Lifecycle
- [alpha] Ensure critical cluster infrastructure pods (Heapster, DNS, etc.) can schedule by evicting regular pods when necessary to make the critical pods schedule. (docs) (kubernetes/features#62)
- [alpha] Simplifies bootstrapping of TLS secured communication between the API server and kubelet. (docs) (kubernetes/features#43)
- [alpha] The
kubeadm tool makes it much easier to bootstrap Kubernetes. (docs) (kubernetes/features#11)
- Federation
- [alpha] Creating a
Federated Ingress is as simple as submitting
an Ingress creation request to the Federation API Server. The
Federation control system then creates and maintains a single
global virtual IP to load balance incoming HTTP(S) traffic across
some or all the registered clusters, across all regions. Google's
GCE L7 LoadBalancer is the first supported implementation, and
is available in this release.
(docs)
(kubernetes/features#82)
- [beta]
Federated Replica Sets create and maintain matching
Replica Sets in some or all clusters in a federation, with the
desired replica count distributed equally or according to
specified per-cluster weights.
(docs)
(kubernetes/features#46)
- [beta]
Federated Secrets are created and kept consistent across all clusters in a federation.
(docs)
(kubernetes/features#68)
- [beta] Federation API server gained support for events and many
federation controllers now report important events.
(docs)
(kubernetes/features#70)
- [alpha] Creating a
Federated Namespace causes matching
Namespaces to be created and maintained in all the clusters registered with that federation. (docs) (kubernetes/features#69)
- [alpha] ingress has alpha support for a single master multi zone cluster (docs) (kubernetes/features#52)
- Network
- Node
- Scheduling
- [alpha] Allows pods to require or prohibit (or prefer or prefer not) co-scheduling on the same node (or zone or other topology domain) as another set of pods. (docs (kubernetes/features#51)
- Storage
- UI
- [stable] Kubernetes Dashboard UI - a great looking Kubernetes Dashboard UI with 90% CLI parity for at-a-glance management. docs
- [stable]
kubectl no longer applies defaults before sending objects to the server in create and update requests, allowing the server to apply the defaults. (kubernetes/features#55)
Known Issues
- Completed pods lose logs across node upgrade (#32324)
- Pods are deleted across node upgrade (#32323)
- Secure master -> node communication (#11816)
- upgrading master doesn't upgrade kubectl (#32538)
- Specific error message on failed rolling update issued by older kubectl against 1.4 master (#32751)
- bump master cidr range from /30 to /29 (#32886)
- non-hostNetwork daemonsets will almost always have a pod that fails to schedule (#32900)
- Service loadBalancerSourceRanges doesn't respect updates (#33033)
- disallow user to update loadbalancerSourceRanges (#33346)
Notable Changes to Existing Behavior
Deployments
- ReplicaSets of paused Deployments are now scaled while the Deployment is paused. This is retroactive to existing Deployments.
- When scaling a Deployment during a rollout, the ReplicaSets of all Deployments are now scaled proportionally based on the number of replicas they each have instead of only scaling the newest ReplicaSet.
kubectl rolling-update: < v1.4.0 client vs >=v1.4.0 cluster
Old version kubectl's rolling-update command is compatible with Kubernetes 1.4 and higher only if you specify a new replication controller name. You will need to update to kubectl 1.4 or higher to use the rolling update command against a 1.4 cluster if you want to keep the original name, or you'll have to do two rolling updates.
If you do happen to use old version kubectl's rolling update against a 1.4 cluster, it will fail, usually with an error message that will direct you here. If you saw that error, then don't worry, the operation succeeded except for the part where the new replication controller is renamed back to the old name. You can just do another rolling update using kubectl 1.4 or higher to change the name back: look for a replication controller that has the original name plus a random suffix.
Unfortunately, there is a much rarer second possible failure mode: the replication controller gets renamed to the old name, but there is a duplicated set of pods in the cluster. kubectl will not report an error since it thinks its job is done.
If this happens to you, you can wait at most 10 minutes for the replication controller to start a resync, the extra pods will then be deleted. Or, you can manually trigger a resync by change the replicas in the spec of the replication controller.
kubectl delete: < v1.4.0 client vs >=v1.4.0 cluster
If you use an old version kubectl to delete a replication controller or replicaset, then after the delete command has returned, the replication controller or the replicaset will continue to exist in the key-value store for a short period of time (<1s). You probably will not notice any difference if you use kubectl manually, but you might notice it if you are using kubectl in a script.
DELETE operation in REST API
-
Replication controller & Replicaset: the DELETE request of a replication controller or a replicaset becomes asynchronous by default. The object will continue to exist in the key-value store for some time. The API server will set its metadata.deletionTimestamp, add the "orphan" finalizer to its metadata.finalizers. The object will be deleted from the key-value store after the garbage collector orphans its dependents. Please refer to this user-guide for more information regarding the garbage collection.
-
Other objects: no changes unless you explicitly request orphaning.
Action Required Before Upgrading
- If you are using Kubernetes to manage
docker containers, please be aware Kubernetes has been validated to work with docker 1.9.1, docker 1.11.2 (#23397), and docker 1.12.0 (#28698)
- If you upgrade your apiserver to 1.4.x but leave your kubelets at 1.3.x, they will not report init container status, but init containers will work properly. Upgrading kubelets to 1.4.x fixes this.
- The NamespaceExists and NamespaceAutoProvision admission controllers have been removed, use the NamespaceLifecycle admission controller instead (#31250, @derekwaynecarr)
- If upgrading Cluster Federation components from 1.3.x, the
federation-apiserver and federation-controller-manager binaries have been folded into hyperkube. Please switch to using that instead. (#29929, @madhusudancs)
- If you are using the PodSecurityPolicy feature (eg:
kubectl get podsecuritypolicy does not error, and returns one or more objects), be aware that init containers have moved from alpha to beta. If there are any pods with the key pods.beta.kubernetes.io/init-containers, then that pod may not have been filtered by the PodSecurityPolicy. You should find such pods and either delete them or audit them to ensure they do not use features that you intend to be blocked by PodSecurityPolicy. (#31026, @erictune)
- If upgrading Cluster Federation components from 1.3.x, please ensure your cluster name is a valid DNS label (#30956, @nikhiljindal)
- kubelet's
--config flag has been deprecated, use --pod-manifest-path instead (#29999, @mtaufen)
- If upgrading Cluster Federation components from 1.3.x, be aware the federation-controller-manager now looks for a different secret name. Run the following to migrate (#28938, @madhusudancs)
kubectl --namespace=federation get secret federation-apiserver-secret -o json | sed 's/federation-apiserver-secret/federation-apiserver-kubeconfig/g' | kubectl create -f -
# optionally, remove the old secret
kubectl delete secret --namespace=federation federation-apiserver-secret
- Kubernetes components no longer handle panics, and instead actively crash. All Kubernetes components should be run by something that actively restarts them. This is true of the default setups, but those with custom environments may need to double-check (#28800, @lavalamp)
- kubelet now defaults to
--cloud-provider=auto-detect, use --cloud-provider='' to preserve previous default of no cloud provider (#28258, @vishh)
Previous Releases Included in v1.4.0
For a detailed list of all changes that were included in this release, please refer to the following CHANGELOG entries:
v1.4.0-beta.11
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
993e785f501d2fa86c9035b55a875c420059b3541a32b5822acf5fefb9a61916 |
Changelog since v1.4.0-beta.10
No notable changes for this release
v1.4.0-beta.10
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
f3f1f0e5cf8234d640c8e9444c73343f04be8685f92b6a1ad66190f84de2e3a7 |
Changelog since v1.4.0-beta.8
Other notable changes
- Remove cpu limits for dns pod to avoid CPU starvation (#33227, @vishh)
- Resolves x509 verification issue with masters dialing nodes when started with --kubelet-certificate-authority (#33141, @liggitt)
- Upgrading Container-VM base image for k8s on GCE. Brief changelog as follows: (#32738, @Amey-D)
-
- Fixed performance regression in veth device driver
-
- Docker and related binaries are statically linked
-
- Fixed the issue of systemd being oom-killable
- Update cAdvisor to v0.24.0 - see the cAdvisor changelog for the full list of changes. (#33052, @timstclair)
v1.4.0-beta.8
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
31701c5c675c137887b58d7914e39b4c8a9c03767c0c3d89198a52f4476278ca |
Changelog since v1.4.0-beta.7
No notable changes for this release
v1.4.0-beta.7
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
51e8f3ebe55cfcfbe582dd6e5ea60ae125d89373477571c0faee70eff51bab31 |
Changelog since v1.4.0-beta.6
Other notable changes
- Use a patched go1.7.1 for building linux/arm (#32517, @luxas)
- Specific error message on failed rolling update issued by older kubectl against 1.4 master (#32751, @caesarxuchao)
v1.4.0-beta.6
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
0b0158e4745663b48c55527247d3e64cc3649f875fa7611fc7b38fa5c3b736bd |
Changelog since v1.4.0-beta.5
Other notable changes
v1.4.0-beta.5
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
ec6b233b0448472e05e6820b8ea1644119ae4f9fe3a1516cf978117c19bad0a9 |
Changelog since v1.4.0-beta.3
Other notable changes
- Bumped Heapster to v1.2.0. (#32649, @piosz)
- Docker digest validation is too strict (#32627, @smarterclayton)
- Added new kubelet flags
--cni-bin-dir and --cni-conf-dir to specify where CNI files are located. (#32151, @bboreham)
- Fixed CNI configuration on GCI platform when using CNI.
- make --runtime-config=api/all=true|false work (#32582, @jlowdermilk)
- AWS: Change default networking for kube-up to kubenet (#32239, @zmerlynn)
v1.3.7
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
ad18566a09ff87b36107c2ea238fa5e20988d7a62c85df9c8598920679fec4a1 |
Changelog since v1.3.6
Other notable changes
- AWS: Add ap-south-1 to list of known AWS regions (#28428, @justinsb)
- Back porting critical vSphere bug fixes to release 1.3 (#31993, @dagnello)
- Back port - Openstack provider allowing more than one service port for lbaas v2 (#32001, @dagnello)
- Fix a bug in kubelet hostport logic which flushes KUBE-MARK-MASQ iptables chain (#32413, @freehan)
- Fixes the panic that occurs in the federation controller manager when registering a GKE cluster to the federation. Fixes issue #30790. (#30940, @madhusudancs)
v1.4.0-beta.3
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
5a6802703c6b0b652e72166a4347fee7899c46205463f6797dc78f8086876465 |
Changelog since v1.4.0-beta.2
No notable changes for this release
Behavior changes caused by enabling the garbage collector
kubectl rolling-update
Old version kubectl's rolling-update command is compatible with Kubernetes 1.4 and higher only if you specify a new replication controller name. You will need to update to kubectl 1.4 or higher to use the rolling update command against a 1.4 cluster if you want to keep the original name, or you'll have to do two rolling updates.
If you do happen to use old version kubectl's rolling update against a 1.4 cluster, it will fail, usually with an error message that will direct you here. If you saw that error, then don't worry, the operation succeeded except for the part where the new replication controller is renamed back to the old name. You can just do another rolling update using kubectl 1.4 or higher to change the name back: look for a replication controller that has the original name plus a random suffix.
Unfortunately, there is a much rarer second possible failure mode: the replication controller gets renamed to the old name, but there is a duplicate set of pods in the cluster. kubectl will not report an error since it thinks its job is done.
If this happens to you, you can wait at most 10 minutes for the replication controller to start a resync, the extra pods will then be deleted. Or, you can manually trigger a resync by change the replicas in the spec of the replication controller.
kubectl delete
If you use an old version kubectl to delete a replication controller or a replicaset, then after the delete command has returned, the replication controller or the replicaset will continue to exist in the key-value store for a short period of time (<1s). You probably will not notice any difference if you use kubectl manually, but you might notice it if you are using kubectl in a script. To fix it, you can poll the API server to confirm the object is deleted.
DELETE operation in REST API
-
Replication controller & Replicaset: the DELETE request of a replication controller or a replicaset becomes asynchronous by default. The object will continue to exist in the key-value store for some time. The API server will set its metadata.deletionTimestamp, add the "orphan" finalizer to its metadata.finalizers. The object will be deleted from the key-value store after the garbage collector orphans its dependents. Please refer to this user-guide for more information regarding the garbage collection.
-
Other objects: no changes unless you explicitly request orphaning.
v1.4.0-beta.2
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
0c6f54eb9059090c88f10a448ed5bcb6ef663abbd76c79281fd8dcb72faa6315 |
Changelog since v1.4.0-beta.1
Other notable changes
- Fix a bug in kubelet hostport logic which flushes KUBE-MARK-MASQ iptables chain (#32413, @freehan)
- Stick to 2.2.1 etcd (#32404, @caesarxuchao)
- Use etcd 2.3.7 (#32359, @wojtek-t)
- AWS: Change default networking for kube-up to kubenet (#32239, @zmerlynn)
- Make sure finalizers prevent deletion on storage that supports graceful deletion (#32351, @caesarxuchao)
- Some components like kube-dns and kube-proxy could fail to load the service account token when started within a pod. Properly handle empty configurations to try loading the service account config. (#31947, @smarterclayton)
- Use federated namespace instead of the bootstrap cluster's namespace in Ingress e2e tests. (#32105, @madhusudancs)
v1.4.0-beta.1
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
837296455933629b6792a8954f2c5b17d55c1149c12b644101f2f02549d06d25 |
Changelog since v1.4.0-alpha.3
Action Required
- The NamespaceExists and NamespaceAutoProvision admission controllers have been removed. (#31250, @derekwaynecarr)
- All cluster operators should use NamespaceLifecycle.
- Federation binaries and their corresponding docker images -
federation-apiserver and federation-controller-manager are now folded in to the hyperkube binary. If you were using one of these binaries or docker images, please switch to using the hyperkube version. Please refer to the federation manifests - federation/manifests/federation-apiserver.yaml and federation/manifests/federation-controller-manager-deployment.yaml for examples. (#29929, @madhusudancs)
- Use upgraded container-vm by default on worker nodes for GCE k8s clusters (#31023, @vishh)
Other notable changes
- Enable kubelet eviction whenever inodes free is < 5% on GCE (#31545, @vishh)
- Move StorageClass to a storage group (#31886, @deads2k)
- Some components like kube-dns and kube-proxy could fail to load the service account token when started within a pod. Properly handle empty configurations to try loading the service account config. (#31947, @smarterclayton)
- Removed comments in json config when using kubectl edit with -o json (#31685, @jellonek)
- fixes invalid null selector issue in sysdig example yaml (#31393, @baldwinSPC)
- Rescheduler which ensures that critical pods are always scheduled enabled by default in GCE. (#31974, @piosz)
- retry oauth token fetch in gce cloudprovider (#32021, @mikedanese)
- Deprecate the old cbr0 and flannel networking modes (#31197, @freehan)
- AWS: fix volume device assignment race condition (#31090, @justinsb)
- The certificates API group has been renamed to certificates.k8s.io (#31887, @liggitt)
- Increase Dashboard UI version to v1.4.0-beta2 (#31518, @bryk)
- Fixed incomplete kubectl bash completion. (#31333, @xingzhou)
- Added liveness probe to Heapster service. (#31878, @mksalawa)
- Adding clusters to the list of valid resources printed by kubectl help (#31719, @nikhiljindal)
- Kubernetes server components using
kubeconfig files no longer default to http://localhost:8080. Administrators must specify a server value in their kubeconfig files. (#30808, @smarterclayton)
- Update influxdb to 0.12 (#31519, @piosz)
- Include security options in the container created event (#31557, @timstclair)
- Federation can now be deployed using the
federation/deploy/deploy.sh script. This script does not depend on any of the development environment shell library/scripts. This is an alternative to the current federation-up.sh/federation-down.sh scripts. Both the scripts are going to co-exist in this release, but the federation-up.sh/federation-down.sh scripts might be removed in a future release in favor of federation/deploy/deploy.sh script. (#30744, @madhusudancs)
- Add get/delete cluster, delete context to kubectl config (#29821, @alexbrand)
- rkt: Force
rkt fetch to fetch from remote to conform the image pull policy. (#31378, @yifan-gu)
- Allow services which use same port, different protocol to use the same nodePort for both (#30253, @AdoHe)
- Handle overlapping deployments gracefully (#30730, @janetkuo)
- Remove environment variables and internal Kubernetes Docker labels from cAdvisor Prometheus metric labels. (#31064, @grobie)
- Old behavior:
-
- environment variables explicitly whitelisted via --docker-env-metadata-whitelist were exported as
container_env_*=*. Default is zero so by default non were exported
-
- all docker labels were exported as
container_label_*=*
- New behavior:
-
- Only
container_name, pod_name, namespace, id, image, and name labels are exposed
-
- no environment variables will be exposed ever via /metrics, even if whitelisted
- Filter duplicate network packets in promiscuous bridge mode (with ebtables) (#28717, @freehan)
- Refactor to simplify the hard-traveled path of the KubeletConfiguration object (#29216, @mtaufen)
- Fix overflow issue in controller-manager rate limiter (#31396, @foxish)
v1.3.6
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
2db7ace2f72a2e162329a6dc969a5a158bb8c5d0f8054c5b1b2b1063aa22020d |
Changelog since v1.3.5
Other notable changes
- Addresses vSphere Volume Attach limits (#29881, @dagnello)
- Increase request timeout based on termination grace period (#31275, @dims)
- Skip safe to detach check if node API object no longer exists (#30737, @saad-ali)
- Nodecontroller doesn't flip readiness on pods if kubeletVersion < 1.2.0 (#30828, @bprashanth)
- Update cadvisor to v0.23.9 to fix a problem where attempting to gather container filesystem usage statistics could result in corrupted devicemapper thin pool storage for Docker. (#30307, @sjenning)
v1.4.0-alpha.3
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
8055f0373e3b6bdee865749ef9bcfc765396a40f39ec2fa3cd31b675d1bbf5d9 |
Changelog since v1.4.0-alpha.2
Action Required
- Moved init-container feature from alpha to beta. (#31026, @erictune)
- Security Action Required:
- This only applies to you if you use the PodSecurityPolicy feature. You are using that feature if
kubectl get podsecuritypolicy returns one or more objects. If it returns an error, you are not using it.
- If there are any pods with the key
pods.beta.kubernetes.io/init-containers, then that pod may not have been filtered by the PodSecurityPolicy. You should find such pods and either delete them or audit them to ensure they do not use features that you intend to be blocked by PodSecurityPolicy.
- Explanation of Feature
- In 1.3, an init container is specified with this annotation key
- on the pod or pod template:
pods.alpha.kubernetes.io/init-containers.
- In 1.4, either that key or this key:
pods.beta.kubernetes.io/init-containers,
- can be used.
- When you GET an object, you will see both annotation keys with the same values.
- You can safely roll back from 1.4 to 1.3, and things with init-containers
- will still work (pods, deployments, etc).
- If you are running 1.3, only use the alpha annotation, or it may be lost when
- rolling forward.
- The status has moved from annotation key
pods.beta.kubernetes.io/init-container-statuses topods.beta.kubernetes.io/init-container-statuses.- Any code that inspects this annotation should be changed to use the new key.
- State of Initialization will continue to be reported in both pods.alpha.kubernetes.io/initialized
- and in
podStatus.conditions.{status: "True", type: Initialized}
- Action required: federation-only: Please update your cluster name to be a valid DNS label. (#30956, @nikhiljindal)
- Updating federation.v1beta1.Cluster API to disallow subdomains as valid cluster names. Only DNS labels are allowed as valid cluster names now.
- [Kubelet] Rename
--config to --pod-manifest-path. --config is deprecated. (#29999, @mtaufen)
Other notable changes
- rkt: Improve support for privileged pod (pod whose all containers are privileged) (#31286, @yifan-gu)
- The pod annotation
security.alpha.kubernetes.io/sysctls now allows customization of namespaced and well isolated kernel parameters (sysctls), starting with kernel.shm_rmid_forced, net.ipv4.ip_local_port_range and net.ipv4.tcp_syncookies for Kubernetes 1.4. (#27180, @sttts)
- The pod annotation
security.alpha.kubernetes.io/unsafe-sysctls allows customization of namespaced sysctls where isolation is unclear. Unsafe sysctls must be enabled at-your-own-risk on the kubelet with the --experimental-allowed-unsafe-sysctls flag. Future versions will improve on resource isolation and more sysctls will be considered safe.
- Increase request timeout based on termination grace period (#31275, @dims)
- Fixed two issues of kubectl bash completion. (#31135, @xingzhou)
- Reduced size of fluentd images. (#31239, @aledbf)
- support Azure data disk volume (#29836, @rootfs)
- fix Openstack provider to allow more than one service port for lbaas v2 (#30649, @dagnello)
- Add kubelet --network-plugin-mtu flag for MTU selection (#30376, @justinsb)
- Let Services preserve client IPs and not double-hop from external LBs (alpha) (#29409, @girishkalele)
- [Kubelet] Optionally consume configuration from named config maps (#30090, @mtaufen)
- [GarbageCollector] Allow per-resource default garbage collection behavior (#30838, @caesarxuchao)
- Action required: If you have a running federation control plane, you will have to ensure that for all federation resources, the corresponding namespace exists in federation control plane. (#31139, @nikhiljindal)
- federation-apiserver now supports NamespaceLifecycle admission control, which is enabled by default. Set the --admission-control flag on the server to change that.
- Configure webhook (#30923, @Q-Lee)
- Federated Ingress Controller (#30419, @quinton-hoole)
- Federation replicaset controller (#29741, @jianhuiz)
- AWS: More ELB attributes via service annotations (#30695, @krancour)
- Impersonate user extra (#30881, @deads2k)
- DNS, Heapster and UI are critical addons (#30995, @piosz)
- AWS: Support HTTP->HTTP mode for ELB (#30563, @knarz)
- kube-up: Allow IP restrictions for SSH and HTTPS API access on AWS. (#27061, @Naddiseo)
- Add readyReplicas to replica sets (#29481, @kargakis)
- The implicit registration of Prometheus metrics for request count and latency have been removed, and a plug-able interface was added. If you were using our client libraries in your own binaries and want these metrics, add the following to your imports in the main package: "k8s.io/pkg/client/metrics/prometheus". (#30638, @krousey)
- Add support for --image-pull-policy to 'kubectl run' (#30614, @AdoHe)
- x509 authenticator: get groups from subject's organization field (#30392, @ericchiang)
- Add initial support for TokenFile to to the client config file. (#29696, @brendandburns)
- update kubectl help output for better organization (#25524, @AdoHe)
- daemonset controller should respect taints (#31020, @mikedanese)
- Implement TLS bootstrap for kubelet using
--experimental-bootstrap-kubeconfig (2nd take) (#30922, @yifan-gu)
- rkt: Support subPath volume mounts feature (#30934, @yifan-gu)
- Return container command exit codes in kubectl run/exec (#26541, @sttts)
- Fix kubectl describe to display a container's resource limit env vars as node allocatable when the limits are not set (#29849, @aveshagarwal)
- The
valueFrom.fieldRef.name field on environment variables in pods and objects with pod templates now allows two additional fields to be used: (#27880, @smarterclayton)
* spec.nodeName will return the name of the node this pod is running on
* spec.serviceAccountName will return the name of the service account this pod is running under
- Adding ImagePolicyWebhook admission controller. (#30631, @ecordell)
- Validate involvedObject.Namespace matches event.Namespace (#30533, @liggitt)
- allow group impersonation (#30803, @deads2k)
- Always return command output for exec probes and kubelet RunInContainer (#30731, @ncdc)
- Enable the garbage collector by default (#30480, @caesarxuchao)
- NONE (#30599, @therc)
- use valid_resources to replace kubectl.PossibleResourceTypes (#30955, @lojies)
- oidc auth provider: don't trim issuer URL (#30944, @ericchiang)
- Add a short
-n for kubectl --namespace (#30630, @silasbw)
- Federated secret controller (#30669, @kshafiee)
- Add Events for operation_executor to show status of mounts, failed/successful to show in describe events (#27778, @screeley44)
- Alpha support for OpenAPI (aka. Swagger 2.0) specification served on /swagger.json (enabled by default) (#30233, @mbohlool)
- Disable linux/ppc64le compilation by default (#30659, @ixdy)
- Implement dynamic provisioning (beta) of PersistentVolumes via StorageClass (#29006, @jsafrane)
- Allow setting permission mode bits on secrets, configmaps and downwardAPI files (#28936, @rata)
- Skip safe to detach check if node API object no longer exists (#30737, @saad-ali)
- The Kubelet now supports the
--require-kubeconfig option which reads all client config from the provided --kubeconfig file and will cause the Kubelet to exit with error code 1 on error. It also forces the Kubelet to use the server URL from the kubeconfig file rather than the --api-servers flag. Without this flag set, a failure to read the kubeconfig file would only result in a warning message. (#30798, @smarterclayton)
- In a future release, the value of this flag will be defaulted to
true.
- Adding container image verification webhook API. (#30241, @Q-Lee)
- Nodecontroller doesn't flip readiness on pods if kubeletVersion < 1.2.0 (#30828, @bprashanth)
- AWS: Handle kube-down case where the LaunchConfig is dangling (#30816, @zmerlynn)
- kubectl will no longer do client-side defaulting on create and replace. (#30250, @krousey)
- Added warning msg for
kubectl get (#28352, @vefimova)
- Removed support for HPA in extensions client. (#30504, @piosz)
- Implement DisruptionController. (#25921, @mml)
- [Kubelet] Check if kubelet is running as uid 0 (#30466, @vishh)
- Fix third party APIResource reporting (#29724, @brendandburns)
- speed up RC scaler (#30383, @deads2k)
- Set pod state as "unknown" when CNI plugin fails (#30137, @nhlfr)
- Cluster Federation components can now be built and deployed using the make command. Please see federation/README.md for details. (#29515, @madhusudancs)
- Adding events to federation control plane (#30421, @nikhiljindal)
- [kubelet] Introduce --protect-kernel-defaults flag to make the tunable behaviour configurable (#27874, @ingvagabund)
- Add support for kube-up.sh to deploy Calico network policy to GCI masters (#29037, @matthewdupre)
- Added 'kubectl top' command showing the resource usage metrics. (#28844, @mksalawa)
- Add basic audit logging (#27087, @soltysh)
- Marked NodePhase deprecated. (#30005, @dchen1107)
- Name the job created by scheduledjob (sj) deterministically with sj's name and a hash of job's scheduled time. (#30420, @janetkuo)
- add metrics for workqueues (#30296, @deads2k)
- Adding ingress resource to federation apiserver (#30112, @nikhiljindal)
- Update Dashboard UI to version v1.1.1 (#30273, @bryk)
- Update etcd 2.2 references to use 3.0.x (#29399, @timothysc)
- HPA: ignore scale targets whose replica count is 0 (#29212, @sjenning)
- Add total inodes to kubelet summary api (#30231, @derekwaynecarr)
- Updates required for juju kubernetes to use the tls-terminated etcd charm. (#30104, @mbruzek)
- Fix PVC.Status.Capacity and AccessModes after binding (#29982, @jsafrane)
- allow a read-only rbd image mounted by multiple pods (#29622, @rootfs)
- [kubelet] Auto-discover node IP if neither cloud provider exists and IP is not explicitly specified (#29907, @luxas)
- kubectl config set-crentials: add arguments for auth providers (#30007, @ericchiang)
- Scheduledjob controller (#29137, @janetkuo)
- add subjectaccessreviews resource (#20573, @deads2k)
- AWS/GCE: Rework use of master name (#30047, @zmerlynn)
- Add density (batch pods creation latency and resource) and resource performance tests to `test-e2e-node' built for Linux only (#30026, @coufon)
- Clean up items from moving local cluster setup guides (#30035, @pwittrock)
- federation: Adding secret API (#29138, @kshafiee)
- Introducing ScheduledJobs as described in the proposal as part of
batch/v2alpha1 version (experimental feature). (#25816, @soltysh)
- Node disk pressure should induce image gc (#29880, @derekwaynecarr)
- oidc authentication plugin: don't trim issuer URLs with trailing slashes (#29860, @ericchiang)
- Allow leading * in ingress hostname (#29204, @aledbf)
- Rewrite service controller to apply best controller pattern (#25189, @mfanjie)
- Fix issue with kubectl annotate when --resource-version is provided. (#29319, @juanvallejo)
- Reverted conversion of influx-db to Pet Set, it is now a Replication Controller. (#30080, @jszczepkowski)
- rbac validation: rules can't combine non-resource URLs and regular resources (#29930, @ericchiang)
- VSAN support for VSphere Volume Plugin (#29172, @abrarshivani)
- Addresses vSphere Volume Attach limits (#29881, @dagnello)
- allow restricting subresource access (#29988, @deads2k)
- Add density (batch pods creation latency and resource) and resource performance tests to `test-e2e-node' (#29764, @coufon)
- Allow Secret & ConfigMap keys to contain caps, dots, and underscores (#25458, @errm)
- allow watching old resources with kubectl (#27392, @sjenning)
- azure: kube-up respects AZURE_RESOURCE_GROUP (#28700, @colemickens)
- Modified influxdb petset to provision persistent volume. (#28840, @jszczepkowski)
- Allow service names up to 63 characters (RFC 1035) (#29523, @fraenkel)
- Change eviction policies in NodeController: (#28897, @gmarek)
-
- add a "partialDisruption" mode, when more than 33% of Nodes in the zone are not Ready
-
- add "fullDisruption" mode, when all Nodes in the zone are not Ready
- Eviction behavior depends on the mode in which NodeController is operating:
-
- if the new state is "partialDisruption" or "fullDisruption" we call a user defined function that returns a new QPS to use (default 1/10 of the default rate, and the default rate respectively),
-
- if the new state is "normal" we resume normal operation (go back to default limiter settings),
-
- if all zones in the cluster are in "fullDisruption" state we stop all evictions.
- Add a flag for
kubectl exposeto set ClusterIP and allow headless services (#28239, @ApsOps)
- Add support to quota pvc storage requests (#28636, @derekwaynecarr)
v1.3.5
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
46be88ce927124f7cef7e280720b42c63051086880b7ebdba298b561dbe19f82 |
Changelog since v1.3.4
Other notable changes
v1.3.4
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
818acc1a8ba61cff434d4c0c5aa3d342d06e6907b565cfd8651b8cfcf3f0a1e6 |
Changelog since v1.3.3
Other notable changes
- NetworkPolicy cherry-pick 1.3 (#29556, @caseydavenport)
- Allow mounts to run in parallel for non-attachable volumes (#28939, @saad-ali)
- add enhanced volume and mount logging for block devices (#24797, @screeley44)
- kube-up: increase download timeout for kubernetes.tar.gz (#29426, @justinsb)
- Fix RBAC authorizer of ServiceAccount (#29071, @albatross0)
- Update docker engine-api to dea108d3aa (#29144, @ronnielai)
- Assume volume is detached if node doesn't exist (#29485, @saad-ali)
- Make PD E2E Tests Wait for Detach to Prevent Kernel Errors (#29031, @saad-ali)
- Fix "PVC Volume not detached if pod deleted via namespace deletion" issue (#29077, @saad-ali)
- append an abac rule for $KUBE_USER. (#29164, @cjcullen)
v1.4.0-alpha.2
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
787ce63a5149a1cb47d14c55450172e3a045d85349682d2e17ff492de9e415b9 |
Changelog since v1.4.0-alpha.1
Action Required
- Federation API server kubeconfig secret consumed by federation-controller-manager has a new name. (#28938, @madhusudancs)
- If you are upgrading your Cluster Federation components from v1.3.x, please run this command to migrate the federation-apiserver-secret to federation-apiserver-kubeconfig serect;
- $ kubectl --namespace=federation get secret federation-apiserver-secret -o json | sed 's/federation-apiserver-secret/federation-apiserver-kubeconfig/g' | kubectl create -f -
- You might also want to delete the old secret using this command:
- $ kubectl delete secret --namespace=federation federation-apiserver-secret
- Stop eating panics (#28800, @lavalamp)
Other notable changes
- Add API for StorageClasses (#29694, @childsb)
- Fix kubectl help command (#29737, @andreykurilin)
- add shorthand cm for configmaps (#29652, @lojies)
- Bump cadvisor dependencies to latest head. (#29492, @Random-Liu)
- If a service of type node port declares multiple ports, quota on "services.nodeports" will charge for each port in the service. (#29457, @derekwaynecarr)
- Add an Azure CloudProvider Implementation (#28821, @colemickens)
- Add support for kubectl create quota command (#28351, @sttts)
- Assume volume is detached if node doesn't exist (#29485, @saad-ali)
- kube-up: increase download timeout for kubernetes.tar.gz (#29426, @justinsb)
- Allow multiple APIs to register for the same API Group (#28414, @brendandburns)
- Fix a problem with multiple APIs clobbering each other in registration. (#28431, @brendandburns)
- Removing images with multiple tags (#29316, @ronnielai)
- add enhanced volume and mount logging for block devices (#24797, @screeley44)
- append an abac rule for $KUBE_USER. (#29164, @cjcullen)
- add tokenreviews endpoint to implement webhook (#28788, @deads2k)
- Fix "PVC Volume not detached if pod deleted via namespace deletion" issue (#29077, @saad-ali)
- Allow mounts to run in parallel for non-attachable volumes (#28939, @saad-ali)
- Fix working_set calculation in kubelet (#29153, @vishh)
- Fix RBAC authorizer of ServiceAccount (#29071, @albatross0)
- kubectl proxy changed to now allow urls to pods with "attach" or "exec" in the pod name (#28765, @nhlfr)
- AWS: Added experimental option to skip zone check (#28417, @kevensen)
- Ubuntu: Enable ssh compression when downloading binaries during cluster creation (#26746, @MHBauer)
- Add extensions/replicaset to federation-apiserver (#24764, @jianhuiz)
- federation: Adding namespaces API (#26298, @nikhiljindal)
- Improve quota controller performance by eliminating unneeded list calls (#29134, @derekwaynecarr)
- Make Daemonset use GeneralPredicates (#28803, @lukaszo)
- Update docker engine-api to dea108d3aa (#29144, @ronnielai)
- Fixing kube-up for CVM masters. (#29140, @maisem)
- Fix logrotate config on GCI (#29139, @adityakali)
- GCE bring-up: Differentiate NODE_TAGS from NODE_INSTANCE_PREFIX (#29141, @zmerlynn)
- hyperkube: fix build for 3rd party registry (again) (#28489, @liyimeng)
- Detect flakes in PR builder e2e runs (#27898, @lavalamp)
- Remove examples moved to docs site (#23513, @erictune)
- Do not query the metadata server to find out if running on GCE. Retry metadata server query for gcr if running on gce. (#28871, @vishh)
- Change maxsize to size in logrotate. (#29128, @bprashanth)
- Change setting "kubectl --record=false" to stop updating the change-cause when a previous change-cause is found. (#28234, @damemi)
- Add "kubectl --overwrite" flag to automatically resolve conflicts between the modified and live configuration using values from the modified configuration. (#26136, @AdoHe)
- Make discovery summarizer call servers in parallel (#26705, @nebril)
- Don't recreate lb cloud resources on kcm restart (#29082, @bprashanth)
- List all nodes and occupy cidr map before starting allocations (#29062, @bprashanth)
- Fix GPU resource validation (#28743, @therc)
- Make PD E2E Tests Wait for Detach to Prevent Kernel Errors (#29031, @saad-ali)
- Scale kube-proxy conntrack limits by cores (new default behavior) (#28876, @thockin)
- [Kubelet] Improving QOS in kubelet by introducing QoS level Cgroups -
--cgroups-per-qos (#27853, @dubstack)
- AWS: Add ap-south-1 to list of known AWS regions (#28428, @justinsb)
- Add RELEASE_INFRA_PUSH related code to support pushes from kubernetes/release. (#28922, @david-mcmahon)
- Fix watch cache filtering (#28966, @liggitt)
- Deprecate deleting-pods-burst ControllerManager flag (#28882, @gmarek)
- Add support for terminal resizing for exec, attach, and run. Note that for Docker, exec sessions (#25273, @ncdc)
- inherit the environment from the primary process, so if the container was created with tty=false,
- that means the exec session's TERM variable will default to "dumb". Users can override this by
- setting TERM=xterm (or whatever is appropriate) to get the correct "smart" terminal behavior.
- Implement alpha version of PreferAvoidPods (#20699, @jiangyaoguo)
- Retry when apiserver fails to listen on insecure port (#28797, @aaronlevy)
- Add SSH_OPTS to config ssh and scp port (#28872, @lojies)
- kube-up: install new Docker pre-requisite (libltdl7) when not in image (#28745, @justinsb)
- Separate rate limiters for Pod evictions for different zones in NodeController (#28843, @gmarek)
- Add --quiet to hide the 'waiting for pods to be running' message in kubectl run (#28801, @janetkuo)
- Controllers doesn't take any actions when being deleted. (#27438, @gmarek)
- Add "deploy" abbrev for deployments to kubectl (#24087, @Frostman)
- --no-header available now for custom-column (#26696, @gitfred)
v1.3.3
Documentation & Examples
Downloads
| binary |
sha256 hash |
| kubernetes.tar.gz |
a92a74a0d3f7d02d01ac2c8dfb5ee2e97b0485819e77b2110eb7c6b7c782478c |
Changelog since v1.3.2
Other notable changes
- Removing images with multiple tags (#29316, @ronnielai)
- kubectl: don't display an empty list when trying to get a single resource that isn't found (#28294, @ncdc)
- Fix working_set calculation in kubelet (#29154, @vishh)
- Don't delete affinity when endpoints are empty (#28655, @freehan)
- GCE bring-up: Differentiate NODE_TAGS from NODE_INSTANCE_PREFIX (#29141, @zmerlynn)
- Fix logrotate config on GCI (#29139, @adityakali)
- Do not query the metadata server to find out if running on GCE. Retry metadata server query for gcr if running on gce. (#28871, @vishh)
- Fix GPU resource validation (#28743, @therc)
- Scale kube-proxy conntrack limits by cores (new default behavior) (#28876, @thockin)
- Don't recreate lb cloud resources on kcm restart (#29082, @bprashanth)
Known Issues
There are a number of known issues that have been found and are being worked on.
Please be aware of them as you test your workloads.
- PVC Volume not detached if pod deleted via namespace deletion (29051)
- Google Compute Engine PD Detach fails if node no longer exists (29358)
- Mounting (only 'default-token') volume takes a long time when creating a batch of pods (parallelization issue) (28616)
- Error while tearing down pod, "device or resource busy" on service account secret (28750)
v1.3.2
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
f46664d04dc2966c77d8727bba57f57b5f917572 |
1a5b0639941054585d0432dd5ce3abc7 |
Changelog since v1.3.1
Other notable changes
v1.3.1
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
5645b12beda22137204439de8260c62c9925f89b |
ae6e9902ec70c1322d9a0a29ef385190 |
Changelog since v1.3.0
Other notable changes
v1.2.6
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
50023455d00af52c41a7158b4bd117b2dfd4a100 |
cf0411bcb620eb13b08b93578efffc43 |
Changelog since v1.2.5
Other notable changes
v1.4.0-alpha.1
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
11a199208c5164a291c1767a1b9e64e45fdea747 |
334f349daf9268d8ac091d7fcc8e4626 |
Changelog since v1.3.0
Experimental Features
- An alpha implementation of the TLS bootstrap API described in docs/proposals/kubelet-tls-bootstrap.md. (#25562, @gtank)
Action Required
- [kubelet] Allow opting out of automatic cloud provider detection in kubelet. By default kubelet will auto-detect cloud providers (#28258, @vishh)
- If you use one of the kube-dns replication controller manifest in
cluster/saltbase/salt/kube-dns, i.e. cluster/saltbase/salt/kube-dns/{skydns-rc.yaml.base,skydns-rc.yaml.in}, either substitute one of __PILLAR__FEDERATIONS__DOMAIN__MAP__ or {{ pillar['federations_domain_map'] }} with the corresponding federation name to domain name value or remove them if you do not support cluster federation at this time. If you plan to substitute the parameter with its value, here is an example for {{ pillar['federations_domain_map'] } (#28132, @madhusudancs)
- pillar['federations_domain_map'] = "- --federations=myfederation=federation.test"
- where
myfederation is the name of the federation and federation.test is the domain name registered for the federation.
- Proportionally scale paused and rolling deployments (#20273, @kargakis)
Other notable changes
- Support --all-namespaces in kubectl describe (#26315, @dims)
- Add checks in Create and Update Cgroup methods (#28566, @dubstack)
- Update coreos node e2e image to a version that uses cgroupfs (#28661, @dubstack)
- Don't delete affinity when endpoints are empty (#28655, @freehan)
- Enable memory based pod evictions by default on the kubelet. (#28607, @derekwaynecarr)
- Trigger pod eviction when available memory falls below 100Mi.
- Enable extensions/v1beta1/NetworkPolicy by default (#28549, @caseydavenport)
- MESOS: Support a pre-installed km binary at a well known, agent-local path (#28447, @k82cn)
- kubectl should print usage at the bottom (#25640, @dims)
- A new command "kubectl config get-contexts" has been added. (#25463, @asalkeld)
- kubectl: ignore only update conflicts in the scaler (#27048, @kargakis)
- Declare out of disk when there is no free inodes (#28176, @ronnielai)
- Includes the number of free inodes in stat summary (#28173, @ronnielai)
- kubectl: don't display an empty list when trying to get a single resource that isn't found (#28294, @ncdc)
- Graceful deletion bumps object's generation (#27269, @gmarek)
- Allow specifying secret data using strings (#28263, @liggitt)
- kubectl help now provides "Did you mean this?" suggestions for typo/invalid command names. (#27049, @andreykurilin)
- Lock all possible kubecfg files at the beginning of ModifyConfig. (#28232, @cjcullen)
- Enable HTTP2 by default (#28114, @timothysc)
- Influxdb migrated to PetSet and PersistentVolumes. (#28109, @jszczepkowski)
- Change references to gs://kubernetes-release/ci (#28193, @zmerlynn)
- Build: Add KUBE_GCS_RELEASE_BUCKET_MIRROR option to push-ci-build.sh (#28172, @zmerlynn)
- Skip multi-zone e2e tests unless provider is GCE, GKE or AWS (#27871, @lukaszo)
- Making DHCP_OPTION_SET_ID creation optional (#27278, @activars)
- Convert service account token controller to use a work queue (#23858, @liggitt)
- Adding OWNERS for federation (#28042, @nikhiljindal)
- Modifying the default container GC policy parameters (#27881, @ronnielai)
- Kubelet can retrieve host IP even when apiserver has not been contacted (#27508, @aaronlevy)
- Add the Patch method to the generated clientset. (#27293, @caesarxuchao)
- let patch use --local flag like
kubectl set image (#26722, @deads2k)
- enable recursive processing in kubectl edit (#25085, @metral)
- Image GC logic should compensate for reserved blocks (#27996, @ronnielai)
- Bump minimum API version for docker to 1.21 (#27208, @yujuhong)
- Adding lock files for kubeconfig updating (#28034, @krousey)
v1.3.0
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
88249c443d438666928379aa7fe865b389ed72ea |
9270f001aef8c03ff5db63456ca9eecc |
Highlights
- Authorization:
- Alpha RBAC authorization API group
- Federation
- federation api group is now beta
- Services from all federated clusters are now registered in Cloud DNS (AWS and GCP).
- Stateful Apps:
- alpha PetSets manage stateful apps
- alpha Init containers provide one-time setup for stateful containers
- Updating:
- Retry Pod/RC updates in kubectl rolling-update.
- Stop 'kubectl drain' deleting pods with local storage.
- Add
kubectl rollout status
- Security/Auth
- L7 LB controller and disk attach controllers run on master, so nodes do not need those privileges.
- Setting TLS1.2 minimum
kubectl create secret tls command- Webhook Token Authenticator
- beta PodSecurityPolicy objects limits use of security-sensitive features by pods.
- Kubectl
- Display line number on JSON errors
- Add flag -t as shorthand for --tty
- Resources
- Improved node stability by optionally evicting pods upon memory pressure - Design Doc
- alpha: NVIDIA GPU support (#24836, @therc)
- Adding loadBalancer services and nodeports services to quota system
Known Issues and Important Steps before Upgrading
The following versions of Docker Engine are supported - v1.10, v1.11
Although v1.9 is still compatible, we recommend upgrading to one of the supported versions.
All prior versions of docker will not be supported.
ThirdPartyResource
If you use ThirdPartyResource objects, they have moved from being namespaced-scoped to be cluster-scoped. Before upgrading to 1.3.0, export and delete any existing ThirdPartyResource objects using a 1.2.x client:
kubectl get thirdpartyresource --all-namespaces -o yaml > tprs.yaml
kubectl delete -f tprs.yaml
After upgrading to 1.3.0, re-register the third party resource objects at the root scope (using a 1.3 server and client):
kubectl create -f tprs.yaml
kubectl
Kubectl flag --container-port flag is deprecated: it will be removed in the future, please use --target-port instead.
kubernetes Core Known Issues
- Kube Proxy crashes infrequently due to a docker bug (#24000)
- This issue can be resolved by restarting docker daemon
- CORS works only in insecure mode (#24086)
- Persistent volume claims gets added incorrectly after being deleted under stress. Happens very infrequently. (#26082)
Docker runtime Known Issues
-
Kernel crash with Aufs storage driver on Debian Jessie (#27885)
-
File descriptors are leaked in docker v1.11 (#275)
-
Additional memory overhead per container in docker v1.11 (#21737)
-
List of upstream fixes for docker v1.10 identified by RedHat
Rkt runtime Known Issues
- A detailed list of known issues can be found here
More Instructions coming soon
Provider-specific Notes
- AWS
- Support for ap-northeast-2 region (Seoul)
- Allow cross-region image pulling with ECR
- More reliable kube-up/kube-down
- Enable ICMP Type 3 Code 4 for ELBs
- ARP caching fix
- Use /dev/xvdXX names
- ELB:
- ELB proxy protocol support
- mixed plaintext/encrypted ports support in ELBs
- SSL support for ELB listeners
- Allow VPC CIDR to be specified (experimental)
- Fix problems with >2 security groups
- GCP:
- Enable using gcr.io as a Docker registry mirror.
- Make bigger master root disks in GCE for large clusters.
- Change default clusterCIDRs from /16 to /14 allowing 1000 Node clusters by default.
- Allow Debian Jessie on GCE.
- Node problem detector addon pod detects and reports kernel deadlocks.
- OpenStack
- VSphere:
Previous Releases Included in v1.3.0
v1.3.0-beta.3
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
9d18964a294f356bfdc841957dcad8ff35ed909c |
ee5fcdf86645135ed132663967876dd6 |
Changelog since v1.3.0-beta.2
Action Required
- [kubelet] Allow opting out of automatic cloud provider detection in kubelet. By default kubelet will auto-detect cloud providers (#28258, @vishh)
- If you use one of the kube-dns replication controller manifest in
cluster/saltbase/salt/kube-dns, i.e. cluster/saltbase/salt/kube-dns/{skydns-rc.yaml.base,skydns-rc.yaml.in}, either substitute one of __PILLAR__FEDERATIONS__DOMAIN__MAP__ or {{ pillar['federations_domain_map'] }} with the corresponding federation name to domain name value or remove them if you do not support cluster federation at this time. If you plan to substitute the parameter with its value, here is an example for {{ pillar['federations_domain_map'] } (#28132, @madhusudancs)
- pillar['federations_domain_map'] = "- --federations=myfederation=federation.test"
- where
myfederation is the name of the federation and federation.test is the domain name registered for the federation.
- federation: Upgrading the groupversion to v1beta1 (#28186, @nikhiljindal)
- Set Dashboard UI version to v1.1.0 (#27869, @bryk)
Other notable changes
- Build: Add KUBE_GCS_RELEASE_BUCKET_MIRROR option to push-ci-build.sh (#28172, @zmerlynn)
- Image GC logic should compensate for reserved blocks (#27996, @ronnielai)
- Bump minimum API version for docker to 1.21 (#27208, @yujuhong)
- Adding lock files for kubeconfig updating (#28034, @krousey)
- federation service controller: fixing the logic to update DNS records (#27999, @quinton-hoole)
- federation: Updating KubeDNS to try finding a local service first for federation query (#27708, @nikhiljindal)
- Support journal logs in fluentd-gcp on GCI (#27981, @a-robinson)
- Copy and display source location prominently on Kubernetes instances (#27985, @maisem)
- Federation e2e support for AWS (#27791, @colhom)
- Copy and display source location prominently on Kubernetes instances (#27840, @zmerlynn)
- AWS/GCE: Spread PetSet volume creation across zones, create GCE volumes in non-master zones (#27553, @justinsb)
- GCE provider: Create TargetPool with 200 instances, then update with rest (#27829, @zmerlynn)
- Add sources to server tarballs. (#27830, @david-mcmahon)
- Retry Pod/RC updates in kubectl rolling-update (#27509, @janetkuo)
- AWS kube-up: Authorize route53 in the IAM policy (#27794, @justinsb)
- Allow conformance tests to run on non-GCE providers (#26932, @aaronlevy)
- AWS kube-up: move to Docker 1.11.2 (#27676, @justinsb)
- Fixed an issue that Deployment may be scaled down further than allowed by maxUnavailable when minReadySeconds is set. (#27728, @janetkuo)
v1.2.5
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
ddf12d7f37dfef25308798d71ad547761d0785ac |
69d770df8fa4eceb57167e34df3962ca |
Changes since v1.2.4
Other notable changes
- Retry Pod/RC updates in kubectl rolling-update (#27509, @janetkuo)
- GCE provider: Create TargetPool with 200 instances, then update with rest (#27865, @zmerlynn)
- GCE provider: Limit Filter calls to regexps rather than large blobs (#27741, @zmerlynn)
- Fix strategic merge diff list diff bug (#26418, @AdoHe)
- AWS: Fix long-standing bug in stringSetToPointers (#26331, @therc)
- AWS kube-up: Increase timeout waiting for docker start (#25405, @justinsb)
- Fix hyperkube flag parsing (#25512, @colhom)
- kubectl rolling-update support for same image (#24645, @jlowdermilk)
- Return "410 Gone" errors via watch stream when using watch cache (#25369, @liggitt)
v1.3.0-beta.2
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
9c95762970b943d6c6547f0841c1e5471148b0e3 |
dc9e8560f24459b2313317b15910bee7 |
Changes since v1.3.0-beta.1
Experimental Features
- Init containers enable pod authors to perform tasks before their normal containers start. Each init container is started in order, and failing containers will prevent the application from starting. (#23666, @smarterclayton)
Other notable changes
- GCE provider: Limit Filter calls to regexps rather than large blobs (#27741, @zmerlynn)
- Show LASTSEEN, the sorting key, as the first column in
kubectl get event output (#27549, @therc)
- GCI: fix kubectl permission issue #27643 (#27740, @andyzheng0831)
- Add federation api and cm servers to hyperkube (#27586, @colhom)
- federation: Creating kubeconfig files to be used for creating secrets for clusters on aws and gke (#27332, @nikhiljindal)
- AWS: Enable ICMP Type 3 Code 4 for ELBs (#27677, @justinsb)
- Bumped Heapster to v1.1.0. (#27542, @piosz)
- Deleting federation-push.sh (#27400, @nikhiljindal)
- Validate-cluster finishes shortly after at most ALLOWED_NOTREADY_NODE… (#26778, @gmarek)
- AWS kube-down: Issue warning if VPC not found (#27518, @justinsb)
- gce/kube-down: Parallelize IGM deletion, batch more (#27302, @zmerlynn)
- Enable dynamic allocation of heapster/eventer cpu request/limit (#27185, @gmarek)
- 'kubectl describe pv' now shows events (#27431, @jsafrane)
- AWS kube-up: set net.ipv4.neigh.default.gc_thresh1=0 to avoid ARP over-caching (#27682, @justinsb)
- AWS volumes: Use /dev/xvdXX names with EC2 (#27628, @justinsb)
- Add a test config variable to specify desired Docker version to run on GCI. (#26813, @wonderfly)
- Check for thin_is binary in path for devicemapper when using ThinPoolWatcher and fix uint64 overflow issue for CPU stats (#27591, @dchen1107)
- Change default value of deleting-pods-burst to 1 (#27606, @gmarek)
- MESOS: fix race condition in contrib/mesos/pkg/queue/delay (#24916, @jdef)
- including federation binaries in the list of images we push during release (#27396, @nikhiljindal)
- fix updatePod() of RS and RC controllers (#27415, @caesarxuchao)
- Change default value of deleting-pods-burst to 1 (#27422, @gmarek)
- A new volume manager was introduced in kubelet that synchronizes volume mount/unmount (and attach/detach, if attach/detach controller is not enabled). (#26801, @saad-ali)
- This eliminates the race conditions between the pod creation loop and the orphaned volumes loops. It also removes the unmount/detach from the
syncPod() path so volume clean up never blocks the syncPod loop.
v1.3.0-beta.1
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
2b54995ee8f52d78dc31c3d7291e8dfa5c809fe7 |
f1022a84c3441cae4ebe1d295470be8f |
Changes since v1.3.0-alpha.5
Action Required
- Fixing logic to generate ExternalHost in genericapiserver (#26796, @nikhiljindal)
- federation: Updating federation-controller-manager to use secret to get federation-apiserver's kubeconfig (#26819, @nikhiljindal)
Other notable changes
- federation: fix dns provider initialization issues (#27252, @mfanjie)
- Updating federation up scripts to work in non e2e setup (#27260, @nikhiljindal)
- version bump for gci to milestone 53 (#27210, @adityakali)
- kubectl apply: retry applying a patch if a version conflict error is encountered (#26557, @AdoHe)
- Revert "Wait for arc.getArchive() to complete before running tests" (#27130, @pwittrock)
- ResourceQuota BestEffort scope aligned with Pod level QoS (#26969, @derekwaynecarr)
- The AWS cloudprovider will cache results from DescribeInstances() if the set of nodes hasn't changed (#26900, @therc)
- GCE provider: Log full contents of long operations (#26962, @zmerlynn)
- Fix system container detection in kubelet on systemd. (#26586, @derekwaynecarr)
- This fixed environments where CPU and Memory Accounting were not enabled on the unit that launched the kubelet or docker from reporting the root cgroup when monitoring usage stats for those components.
- New default horizontalpodautoscaler/v1 generator for kubectl autoscale. (#26775, @piosz)
- Use autoscaling/v1 in kubectl by default.
- federation: Adding dnsprovider flags to federation-controller-manager (#27158, @nikhiljindal)
- federation service controller: fixing a bug so that existing services are created in newly registered clusters (#27028, @mfanjie)
- Rename environment variables (KUBE_)ENABLE_NODE_AUTOSCALER to (KUBE_)ENABLE_CLUSTER_AUTOSCALER. (#27117, @mwielgus)
- support for mounting local-ssds on GCI (#27143, @adityakali)
- AWS: support mixed plaintext/encrypted ports in ELBs via service.beta.kubernetes.io/aws-load-balancer-ssl-ports annotation (#26976, @therc)
- Updating e2e docs with instructions on running federation tests (#27072, @colhom)
- LBaaS v2 Support for Openstack Cloud Provider Plugin (#25987, @dagnello)
- GCI: add support for network plugin (#27027, @andyzheng0831)
- Bump cAdvisor to v0.23.3 (#27065, @timstclair)
- Stop 'kubectl drain' deleting pods with local storage. (#26667, @mml)
- Networking e2es: Wait for all nodes to be schedulable in kubeproxy and networking tests (#27008, @zmerlynn)
- change clientset of service controller to versioned (#26694, @mfanjie)
- Use gcr.io as a Docker registry mirror when setting up a cluster in GCE. (#25841, @ojarjur)
- correction on rbd volume object and defaults (#25490, @rootfs)
- Bump GCE debian image to container-v1-3-v20160604 (#26851, @zmerlynn)
- Option to enable http2 on client connections. (#25280, @timothysc)
- kubectl get ingress output remove rules (#26684, @AdoHe)
- AWS kube-up: Remove SecurityContextDeny admission controller (to mirror GCE) (#25381, @zquestz)
- Fix third party (#25894, @brendandburns)
- AWS Route53 dnsprovider (#26049, @quinton-hoole)
- GCI/Trusty: support the Docker registry mirror (#26745, @andyzheng0831)
- Kubernetes v1.3 introduces a new Attach/Detach Controller. This controller manages attaching and detaching of volumes on-behalf of nodes. (#26351, @saad-ali)
- This ensures that attachment and detachment of volumes is independent of any single nodes’ availability. Meaning, if a node or kubelet becomes unavailable for any reason, the volumes attached to that node will be detached so they are free to be attached to other nodes.
- Specifically the new controller watches the API server for scheduled pods. It processes each pod and ensures that any volumes that implement the volume Attacher interface are attached to the node their pod is scheduled to.
- When a pod is deleted, the controller waits for the volume to be safely unmounted by kubelet. It does this by waiting for the volume to no longer be present in the nodes Node.Status.VolumesInUse list. If the volume is not safely unmounted by kubelet within a pre-configured duration (3 minutes in Kubernetes v1.3), the controller unilaterally detaches the volume (this prevents volumes from getting stranded on nodes that become unavailable).
- In order to remain backwards compatible, the new controller only manages attach/detach of volumes that are scheduled to nodes that opt-in to controller management. Nodes running v1.3 or higher of Kubernetes opt-in to controller management by default by setting the "volumes.kubernetes.io/controller-managed-attach-detach" annotation on the Node object on startup. This behavior is gated by a new kubelet flag, "enable-controller-attach-detach,” (default true).
- In order to safely upgrade an existing Kubernetes cluster without interruption of volume attach/detach logic:
- First upgrade the master to Kubernetes v1.3.
- This will start the new attach/detach controller.
- The new controller will initially ignore volumes for all nodes since they lack the "volumes.kubernetes.io/controller-managed-attach-detach" annotation.
- Then upgrade nodes to Kubernetes v1.3.
- As nodes are upgraded, they will automatically, by default, opt-in to attach/detach controller management, which will cause the controller to start managing attaches/detaches for volumes that get scheduled to those nodes.
- Added DNS Reverse Record logic for service IPs (#26226, @ArtfulCoder)
- read gluster log to surface glusterfs plugin errors properly in describe events (#24808, @screeley44)
v1.3.0-alpha.5
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
724bf5a4437ca9dc75d9297382f47a179e8dc5a6 |
2a8b4a5297df3007fce69f1e344fd87e |
Changes since v1.3.0-alpha.4
Action Required
Other notable changes
- Fix a bug with pluralization of third party resources (#25374, @brendandburns)
- Run l7 controller on master (#26048, @bprashanth)
- AWS: ELB proxy protocol support via annotation service.beta.kubernetes.io/aws-load-balancer-proxy-protocol (#24569, @williamsandrew)
- kubectl run --restart=Never creates pods (#25253, @soltysh)
- Add LabelSelector to PersistentVolumeClaimSpec (#25917, @pmorie)
- Removed metrics api group (#26073, @piosz)
- Fixed check in kubectl autoscale: cpu consumption can be higher than 100%. (#26162, @jszczepkowski)
- Add support for 3rd party objects to kubectl label (#24882, @brendandburns)
- Move shell completion generation into 'kubectl completion' command (#23801, @sttts)
- Fix strategic merge diff list diff bug (#26418, @AdoHe)
- Setting TLS1.2 minimum because TLS1.0 and TLS1.1 are vulnerable (#26169, @victorgp)
- Kubelet: Periodically reporting image pulling progress in log (#26145, @Random-Liu)
- Federation service controller is one key component of federation controller manager, it watches federation service, creates/updates services to all registered clusters, and update DNS records to global DNS server. (#26034, @mfanjie)
- Stabilize map order in kubectl describe (#26046, @timoreimann)
- Google Cloud DNS dnsprovider - replacement for #25389 (#26020, @quinton-hoole)
- Fix system container detection in kubelet on systemd. (#25982, @derekwaynecarr)
- This fixed environments where CPU and Memory Accounting were not enabled on the unit
- that launched the kubelet or docker from reporting the root cgroup when
- monitoring usage stats for those components.
- Added pods-per-core to kubelet. #25762 (#25813, @rrati)
- promote sourceRange into service spec (#25826, @freehan)
- kube-controller-manager: Add configure-cloud-routes option (#25614, @justinsb)
- kubelet: reading cloudinfo from cadvisor (#21373, @enoodle)
- Disable cAdvisor event storage by default (#24771, @timstclair)
- Remove docker-multinode (#26031, @luxas)
- nodecontroller: Fix log message on successful update (#26207, @zmerlynn)
- remove deprecated generated typed clients (#26336, @caesarxuchao)
- Kubenet host-port support through iptables (#25604, @freehan)
- Add metrics support for a GCE PD, EC2 EBS & Azure File volumes (#25852, @vishh)
- Bump cAdvisor to v0.23.2 - See changelog for details (#25914, @timstclair)
- Alpha version of "Role Based Access Control" API. (#25634, @ericchiang)
- Add Seccomp API (#25324, @jfrazelle)
- AWS: Fix long-standing bug in stringSetToPointers (#26331, @therc)
- Add dnsmasq as a DNS cache in kube-dns pod (#26114, @ArtfulCoder)
- routecontroller: Add wait.NonSlidingUntil, use it (#26301, @zmerlynn)
- Attempt 2: Bump GCE containerVM to container-v1-3-v20160517 (Docker 1.11.1) again. (#26001, @dchen1107)
- Downward API implementation for resources limits and requests (#24179, @aveshagarwal)
- GCE clusters start using GCI as the default OS image for masters (#26197, @wonderfly)
- Add a 'kubectl clusterinfo dump' option (#20672, @brendandburns)
- Fixing heapster memory requirements. (#26109, @Q-Lee)
- Handle federated service name lookups in kube-dns. (#25727, @madhusudancs)
- Support sort-by timestamp in kubectl get (#25600, @janetkuo)
- vSphere Volume Plugin Implementation (#24947, @abithap)
- ResourceQuota controller uses rate limiter to prevent hot-loops in error situations (#25748, @derekwaynecarr)
- Fix hyperkube flag parsing (#25512, @colhom)
- Add a kubectl create secret tls command (#24719, @bprashanth)
- Introduce a new add-on pod NodeProblemDetector. (#25986, @Random-Liu)
- NodeProblemDetector is a DaemonSet running on each node, monitoring node health and reporting
- node problems as NodeCondition and Event. Currently it already supports kernel log monitoring, and
- will support more problem detection in the future. It is enabled by default on gce now.
- Handle cAdvisor partial failures (#25933, @timstclair)
- Use SkyDNS as a library for a more integrated kube DNS (#23930, @ArtfulCoder)
- Introduce node memory pressure condition to scheduler (#25531, @ingvagabund)
- Fix detection of docker cgroup on RHEL (#25907, @ncdc)
- Kubelet evicts pods when available memory falls below configured eviction thresholds (#25772, @derekwaynecarr)
- Use protobufs by default to communicate with apiserver (still store JSONs in etcd) (#25738, @wojtek-t)
- Implement NetworkPolicy v1beta1 API object / client support. (#25638, @caseydavenport)
- Only expose top N images in
NodeStatus (#25328, @resouer)
- Extend secrets volumes with path control (#25285, @ingvagabund)
- With this PR, kubectl and other RestClient's using the AuthProvider framework can make OIDC authenticated requests, and, if there is a refresh token present, the tokens will be refreshed as needed. (#25270, @bobbyrullo)
- Make addon-manager cross-platform and use it with hyperkube (#25631, @luxas)
- kubelet: Optionally, have kubelet exit if lock file contention is observed, using --exit-on-lock-contention flag (#25596, @derekparker)
- Bump up glbc version to 0.6.2 (#25446, @bprashanth)
- Add "kubectl set image" for easier updating container images (for pods or resources with pod templates). (#25509, @janetkuo)
- NodeController doesn't evict Pods if no Nodes are Ready (#25571, @gmarek)
- Incompatible change of kube-up.sh: (#25734, @jszczepkowski)
- when turning on cluster autoscaler by setting KUBE_ENABLE_NODE_AUTOSCALER=true,
- KUBE_AUTOSCALER_MIN_NODES and KUBE_AUTOSCALER_MAX_NODES need to be set.
- systemd node spec proposal (#17688, @derekwaynecarr)
- Bump GCE ContainerVM to container-v1-3-v20160517 (Docker 1.11.1) (#25843, @zmerlynn)
- AWS: Move enforcement of attached AWS device limit from kubelet to scheduler (#23254, @jsafrane)
- Refactor persistent volume controller (#24331, @jsafrane)
- Add support for running GCI on the GCE cloud provider (#25425, @andyzheng0831)
- Implement taints and tolerations (#24134, @kevin-wangzefeng)
- Add init containers to pods (#23567, @smarterclayton)
v1.3.0-alpha.4
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
758e97e7e50153840379ecd9f8fda1869543539f |
4e18ae6a428c99fcc30e2137d7c41854 |
Changes since v1.3.0-alpha.3
Action Required
Other notable changes
- Fix hyperkube's layer caching, and remove --make-symlinks at build time (#25693, @luxas)
- AWS: More support for ap-northeast-2 region (#24464, @matthewrudy)
- Make bigger master root disks in GCE for large clusters (#25670, @gmarek)
- AWS kube-down: don't fail if ELB not in VPC - #23784 (#23785, @ajohnstone)
- Build hyperkube in hack/local-up-cluster instead of separate binaries (#25627, @luxas)
- enable recursive processing in kubectl rollout (#25110, @metral)
- Support struct,array,slice types when sorting kubectl output (#25022, @zhouhaibing089)
- federated api servers: Adding a discovery summarizer server (#20358, @nikhiljindal)
- AWS: Allow cross-region image pulling with ECR (#24369, @therc)
- Automatically add node labels beta.kubernetes.io/{os,arch} (#23684, @luxas)
- kubectl "rm" will suggest using "delete"; "ps" and "list" will suggest "get". (#25181, @janetkuo)
- Add IPv6 address support for pods - does NOT include services (#23090, @tgraf)
- Use local disk for ConfigMap volume instead of tmpfs (#25306, @pmorie)
- Alpha support for scheduling pods on machines with NVIDIA GPUs whose kubelets use the
--experimental-nvidia-gpus flag, using the alpha.kubernetes.io/nvidia-gpu resource (#24836, @therc)
- AWS: SSL support for ELB listeners through annotations (#23495, @therc)
- Implement
kubectl rollout status that can be used to watch a deployment's rollout status (#19946, @janetkuo)
- Webhook Token Authenticator (#24902, @cjcullen)
- Update PodSecurityPolicy types and add admission controller that could enforce them (#24600, @pweil-)
- Introducing ScheduledJobs as described in the proposal as part of
batch/v2alpha1 version (experimental feature). (#24970, @soltysh)
- kubectl now supports validation of nested objects with different ApiGroups (e.g. objects in a List) (#25172, @pwittrock)
- Change default clusterCIDRs from /16 to /14 in GCE configs allowing 1000 Node clusters by default. (#25350, @gmarek)
- Add 'kubectl set' (#25444, @janetkuo)
- vSphere Cloud Provider Implementation (#24703, @dagnello)
- Added JobTemplate, a preliminary step for ScheduledJob and Workflow (#21675, @soltysh)
- Openstack provider (#21737, @zreigz)
- AWS kube-up: Allow VPC CIDR to be specified (experimental) (#23362, @miguelfrde)
- Return "410 Gone" errors via watch stream when using watch cache (#25369, @liggitt)
- GKE provider: Add cluster-ipv4-cidr and arbitrary flags (#25437, @zmerlynn)
- AWS kube-up: Increase timeout waiting for docker start (#25405, @justinsb)
- Sort resources in quota errors to avoid duplicate events (#25161, @derekwaynecarr)
- Display line number on JSON errors (#25038, @mfojtik)
- If the cluster node count exceeds the GCE TargetPool maximum (currently 1000), (#25178, @zmerlynn)
- randomly select which nodes are members of Kubernetes External Load Balancers.
- Clarify supported version skew between masters, nodes, and clients (#25087, @ihmccreery)
- Move godeps to vendor/ (#24242, @thockin)
- Introduce events flag for describers (#24554, @ingvagabund)
- run kube-addon-manager in a static pod (#23600, @mikedanese)
- Reimplement 'pause' in C - smaller footprint all around (#23009, @uluyol)
- Add subPath to mount a child dir or file of a volumeMount (#22575, @MikaelCluseau)
- Handle image digests in node status and image GC (#25088, @ncdc)
- PLEG: reinspect pods that failed prior inspections (#25077, @ncdc)
- Fix kubectl create secret/configmap to allow = values (#24989, @derekwaynecarr)
- Upgrade installed packages when building hyperkube to improve the security profile (#25114, @aaronlevy)
- GCI/Trusty: Support ABAC authorization (#24950, @andyzheng0831)
- fix cinder volume dir umount issue #24717 (#24718, @chengyli)
- Inter pod topological affinity and anti-affinity implementation (#22985, @kevin-wangzefeng)
- start etcd compactor in background (#25010, @hongchaodeng)
- GCI: Add two GCI specific metadata pairs (#25105, @andyzheng0831)
- Ensure status is not changed during an update of PV, PVC, HPA objects (#24924, @mqliang)
- GCE: Prefer preconfigured node tags for firewalls, if available (#25148, @a-robinson)
- kubectl rolling-update support for same image (#24645, @jlowdermilk)
- Add an entry to the salt config to allow Debian jessie on GCE. (#25123, @jlewi)
- As with the existing Wheezy image on GCE, docker is expected
- to already be installed in the image.
- Mark kube-push.sh as broken (#25095, @ihmccreery)
- AWS: Add support for ap-northeast-2 region (Seoul) (#24457, @leokhoa)
- GCI: Update the command to get the image (#24987, @andyzheng0831)
- Port-forward: use out and error streams instead of glog (#17030, @csrwng)
- Promote Pod Hostname & Subdomain to fields (were annotations) (#24362, @ArtfulCoder)
- Validate deletion timestamp doesn't change on update (#24839, @liggitt)
- Add flag -t as shorthand for --tty (#24365, @janetkuo)
- Add support for running clusters on GCI (#24893, @andyzheng0831)
- Switch to ABAC authorization from AllowAll (#24210, @cjcullen)
- Fix DeletingLoadBalancer event generation. (#24833, @a-robinson)
v1.2.4
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
f3aea83f8f0e16b2b41998a2edc09eb42fd8d945 |
ab0aca3a20e8eba43c8ff9d672793618 |
Changes since v1.2.3
Other notable changes
- Ensure status is not changed during an update of PV, PVC, HPA objects (#24924, @mqliang)
- GCI: Add two GCI specific metadata pairs (#25105, @andyzheng0831)
- Add an entry to the salt config to allow Debian jessie on GCE. (#25123, @jlewi)
- As with the existing Wheezy image on GCE, docker is expected
- to already be installed in the image.
- Fix DeletingLoadBalancer event generation. (#24833, @a-robinson)
- GCE: Prefer preconfigured node tags for firewalls, if available (#25148, @a-robinson)
- Drain pods created from ReplicaSets in 'kubectl drain' (#23689, @maclof)
- GCI: Update the command to get the image (#24987, @andyzheng0831)
- Validate deletion timestamp doesn't change on update (#24839, @liggitt)
- Add support for running clusters on GCI (#24893, @andyzheng0831)
- Trusty: Add retry in curl commands (#24749, @andyzheng0831)
v1.3.0-alpha.3
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
01e0dc68653173614dc99f44875173478f837b38 |
ae22c35f3a963743d21daa17683e0288 |
Changes since v1.3.0-alpha.2
Action Required
- Updating go-restful to generate "type":"object" instead of "type":"any" in swagger-spec (breaks kubectl 1.1) (#22897, @nikhiljindal)
- Make watch cache treat resourceVersion consistent with uncached watch (#24008, @liggitt)
Other notable changes
- Trusty: Add retry in curl commands (#24749, @andyzheng0831)
- Collect and expose runtime's image storage usage via Kubelet's /stats/summary endpoint (#23595, @vishh)
- Adding loadBalancer services to quota system (#24247, @sdminonne)
- Enforce --max-pods in kubelet admission; previously was only enforced in scheduler (#24674, @gmarek)
- All clients under ClientSet share one RateLimiter. (#24166, @gmarek)
- Remove requirement that Endpoints IPs be IPv4 (#23317, @aanm)
- Fix unintended change of Service.spec.ports[].nodePort during kubectl apply (#24180, @AdoHe)
- Don't log private SSH key (#24506, @timstclair)
- Incremental improvements to kubelet e2e tests (#24426, @pwittrock)
- Bridge off-cluster traffic into services by masquerading. (#24429, @cjcullen)
- Flush conntrack state for removed/changed UDP Services (#22573, @freehan)
- Allow setting the Host header in a httpGet probe (#24292, @errm)
- Fix goroutine leak in ssh-tunnel healthcheck. (#24487, @cjcullen)
- Fix gce.getDiskByNameUnknownZone logic. (#24452, @a-robinson)
- Make etcd cache size configurable (#23914, @jsravn)
- Drain pods created from ReplicaSets in 'kubectl drain' (#23689, @maclof)
- Make kubectl edit not convert GV on edits (#23437, @DirectXMan12)
- don't ship kube-registry-proxy and pause images in tars. (#23605, @mikedanese)
- Do not throw creation errors for containers that fail immediately after being started (#23894, @vishh)
- Add a client flag to delete "--now" for grace period 0 (#23756, @smarterclayton)
- add act-as powers (#23549, @deads2k)
- Build Kubernetes, etcd and flannel for arm64 and ppc64le (#23931, @luxas)
- Honor starting resourceVersion in watch cache (#24208, @ncdc)
- Update the pause image to build for arm64 and ppc64le (#23697, @luxas)
- Return more useful error information when a persistent volume fails to mount (#23122, @screeley44)
- Trusty: Avoid unnecessary in-memory temp files (#24144, @andyzheng0831)
- e2e: fix error checking in kubelet stats (#24205, @yujuhong)
- Fixed mounting with containerized kubelet (#23435, @jsafrane)
- Adding nodeports services to quota (#22154, @sdminonne)
- e2e: adapt kubelet_perf.go to use the new summary metrics API (#24003, @yujuhong)
- kubelet: add RSS memory to the summary API (#24015, @yujuhong)
v1.2.3
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
b2ce4e0c72562d09ba06e3c0913f0bd78da0285e |
69e75650de30d5a52d144799e94a168d |
Changes since v1.2.2
Action Required
- Make watch cache treat resourceVersion consistent with uncached watch (#24008, @liggitt)
Other notable changes
- Fix unintended change of Service.spec.ports[].nodePort during kubectl apply (#24180, @AdoHe)
- Flush conntrack state for removed/changed UDP Services (#22573, @freehan)
- Allow setting the Host header in a httpGet probe (#24292, @errm)
- Bridge off-cluster traffic into services by masquerading. (#24429, @cjcullen)
- Version-guard Kubectl client Guestbook application test against deployments (#24478, @ihmccreery)
- Fix goroutine leak in ssh-tunnel healthcheck. (#24487, @cjcullen)
- Fixed mounting with containerized kubelet (#23435, @jsafrane)
- Do not throw creation errors for containers that fail immediately after being started (#23894, @vishh)
- Honor starting resourceVersion in watch cache (#24208, @ncdc)
- Fix TerminationMessagePath (#23658, @Random-Liu)
- Fix gce.getDiskByNameUnknownZone logic. (#24452, @a-robinson)
- kubelet: add RSS memory to the summary API (#24015, @yujuhong)
- e2e: adapt kubelet_perf.go to use the new summary metrics API (#24003, @yujuhong)
- e2e: fix error checking in kubelet stats (#24205, @yujuhong)
- Trusty: Avoid unnecessary in-memory temp files (#24144, @andyzheng0831)
- Allowing type object in kubectl swagger validation (#24054, @nikhiljindal)
- Add ClusterUpgrade tests (#24150, @ihmccreery)
- Trusty: Do not create the docker-daemon cgroup (#23996, @andyzheng0831)
v1.3.0-alpha.2
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
305c8c2af7e99d463dbbe4208ecfe2b50585e796 |
aadb8d729d855e69212008f8fda628c0 |
Changes since v1.3.0-alpha.1
Other notable changes
- Make kube2sky and skydns docker images cross-platform (#19376, @luxas)
- Allowing type object in kubectl swagger validation (#24054, @nikhiljindal)
- Fix TerminationMessagePath (#23658, @Random-Liu)
- Trusty: Do not create the docker-daemon cgroup (#23996, @andyzheng0831)
- Make ConfigMap volume readable as non-root (#23793, @pmorie)
- only include running and pending pods in daemonset should place calculation (#23929, @mikedanese)
- Upgrade to golang 1.6 (#22149, @luxas)
- Cross-build hyperkube and debian-iptables for ARM. Also add a flannel image (#21617, @luxas)
- Add a timeout to the sshDialer to prevent indefinite hangs. (#23843, @cjcullen)
- Ensure object returned by volume getCloudProvider incorporates cloud config (#23769, @saad-ali)
- Update Dashboard UI addon to v1.0.1 (#23724, @maciaszczykm)
- Add zsh completion for kubectl (#23797, @sttts)
- AWS kube-up: tolerate a lack of ephemeral volumes (#23776, @justinsb)
- duplicate kube-apiserver to federated-apiserver (#23509, @jianhuiz)
- Kubelet: Start using the official docker engine-api (#23506, @Random-Liu)
- Fix so setup-files don't recreate/invalidate certificates that already exist (#23550, @luxas)
- A pod never terminated if a container image registry was unavailable (#23746, @derekwaynecarr)
- Fix jsonpath to handle maps with key of nonstring types (#23358, @aveshagarwal)
- Trusty: Regional release .tar.gz support (#23558, @andyzheng0831)
- Add support for 3rd party objects to kubectl (#18835, @brendandburns)
- Remove unnecessary override of /etc/init.d/docker on containervm image. (#23593, @dchen1107)
- make docker-checker more robust (#23662, @ArtfulCoder)
- Change kube-proxy & fluentd CPU request to 20m/80m. (#23646, @cjcullen)
- Create a new Deployment in kube-system for every version. (#23512, @Q-Lee)
- IngressTLS: allow secretName to be blank for SNI routing (#23500, @tam7t)
- don't sync deployment when pod selector is empty (#23467, @mikedanese)
- AWS: Fix problems with >2 security groups (#23340, @justinsb)
v1.2.2
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
8dede5833a1986434adea80749624f81a0db7bb4 |
72a5389f22827fb5133fdc3b7bfb9b3a |
Changes since v1.2.1
Other notable changes
- Trusty: Update heapster manifest handling code (#23434, @andyzheng0831)
- Support addon Deployments, make heapster a deployment with a nanny. (#22893, @Q-Lee)
- Create a new Deployment in kube-system for every version. (#23512, @Q-Lee)
- Use SCP to dump logs and parallelize a bit. (#22835, @spxtr)
- Trusty: Regional release .tar.gz support (#23558, @andyzheng0831)
- Make ConfigMap volume readable as non-root (#23793, @pmorie)
- only include running and pending pods in daemonset should place calculation (#23929, @mikedanese)
- A pod never terminated if a container image registry was unavailable (#23746, @derekwaynecarr)
- Update Dashboard UI addon to v1.0.1 (#23724, @maciaszczykm)
- Ensure object returned by volume getCloudProvider incorporates cloud config (#23769, @saad-ali)
- Add a timeout to the sshDialer to prevent indefinite hangs. (#23843, @cjcullen)
- AWS kube-up: tolerate a lack of ephemeral volumes (#23776, @justinsb)
- Fix so setup-files don't recreate/invalidate certificates that already exist (#23550, @luxas)
v1.2.1
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
1639807c5788e1c6b1ab51fd30b723fb5debd865 |
235a1da47972c96a560d718d3256ca4f |
Changes since v1.2.0
Other notable changes
- AWS: Fix problems with >2 security groups (#23340, @justinsb)
- IngressTLS: allow secretName to be blank for SNI routing (#23500, @tam7t)
- Heapster patch release to 1.0.2 (#23487, @piosz)
- Remove unnecessary override of /etc/init.d/docker on containervm image. (#23593, @dchen1107)
- Change kube-proxy & fluentd CPU request to 20m/80m. (#23646, @cjcullen)
- make docker-checker more robust (#23662, @ArtfulCoder)
- validate that daemonsets don't have empty selectors on creation (#23530, @mikedanese)
- don't sync deployment when pod selector is empty (#23467, @mikedanese)
- Support differentiation of OS distro in e2e tests (#23466, @andyzheng0831)
- don't sync daemonsets with selectors that match all pods (#23223, @mikedanese)
- Trusty: Avoid reaching GCE custom metadata size limit (#22818, @andyzheng0831)
- Update kubectl help for 1.2 resources (#23305, @janetkuo)
- Removing URL query param from swagger UI to fix the XSS issue (#23234, @nikhiljindal)
- Fix hairpin mode (#23325, @MurgaNikolay)
- Bump to container-vm-v20160321 (#23313, @zmerlynn)
- Remove the restart-kube-proxy and restart-apiserver functions (#23180, @roberthbailey)
- Copy annotations back from RS to Deployment on rollback (#23160, @janetkuo)
- Trusty: Support hybrid cluster with nodes on ContainerVM (#23079, @andyzheng0831)
- update expose command description to add deployment (#23246, @AdoHe)
- Add a rate limiter to the GCE cloudprovider (#23019, @alex-mohr)
- Add a Deployment example for kubectl expose. (#23222, @madhusudancs)
- Use versioned object when computing patch (#23145, @liggitt)
- kubelet: send all recevied pods in one update (#23141, @yujuhong)
- Add a SSHKey sync check to the master's healthz (when using SSHTunnels). (#23167, @cjcullen)
- Validate minimum CPU limits to be >= 10m (#23143, @vishh)
- Fix controller-manager race condition issue which cause endpoints flush during restart (#23035, @xinxiaogang)
- MESOS: forward globally declared cadvisor housekeeping flags (#22974, @jdef)
- Trusty: support developer workflow on base image (#22960, @andyzheng0831)
v1.3.0-alpha.1
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
e0041b08e220a4704ea2ad90a6ec7c8f2120c2d3 |
7bb2df32aea94678f72a8d1f43a12098 |
Changes since v1.2.0
Action Required
- Disabling swagger ui by default on apiserver. Adding a flag that can enable it (#23025, @nikhiljindal)
- restore ability to run against secured etcd (#21535, @AdoHe)
Other notable changes
- validate that daemonsets don't have empty selectors on creation (#23530, @mikedanese)
- Trusty: Update heapster manifest handling code (#23434, @andyzheng0831)
- Support differentiation of OS distro in e2e tests (#23466, @andyzheng0831)
- don't sync daemonsets with selectors that match all pods (#23223, @mikedanese)
- Trusty: Avoid reaching GCE custom metadata size limit (#22818, @andyzheng0831)
- Update kubectl help for 1.2 resources (#23305, @janetkuo)
- Support addon Deployments, make heapster a deployment with a nanny. (#22893, @Q-Lee)
- Removing URL query param from swagger UI to fix the XSS issue (#23234, @nikhiljindal)
- Fix hairpin mode (#23325, @MurgaNikolay)
- Bump to container-vm-v20160321 (#23313, @zmerlynn)
- Remove the restart-kube-proxy and restart-apiserver functions (#23180, @roberthbailey)
- Copy annotations back from RS to Deployment on rollback (#23160, @janetkuo)
- Trusty: Support hybrid cluster with nodes on ContainerVM (#23079, @andyzheng0831)
- update expose command description to add deployment (#23246, @AdoHe)
- Add a rate limiter to the GCE cloudprovider (#23019, @alex-mohr)
- Add a Deployment example for kubectl expose. (#23222, @madhusudancs)
- Use versioned object when computing patch (#23145, @liggitt)
- kubelet: send all recevied pods in one update (#23141, @yujuhong)
- Add a SSHKey sync check to the master's healthz (when using SSHTunnels). (#23167, @cjcullen)
- Validate minimum CPU limits to be >= 10m (#23143, @vishh)
- Fix controller-manager race condition issue which cause endpoints flush during restart (#23035, @xinxiaogang)
- MESOS: forward globally declared cadvisor housekeeping flags (#22974, @jdef)
- Trusty: support developer workflow on base image (#22960, @andyzheng0831)
- Bumped Heapster to stable version 1.0.0 (#22993, @piosz)
- Deprecating --api-version flag (#22410, @nikhiljindal)
- allow resource.version.group in kubectl (#22853, @deads2k)
- Use SCP to dump logs and parallelize a bit. (#22835, @spxtr)
- update wide option output (#22772, @AdoHe)
- Change scheduler logic from random to round-robin (#22430, @gmarek)
v1.2.0
Documentation & Examples
Downloads
| binary |
sha1 hash |
md5 hash |
| kubernetes.tar.gz |
52dd998e1191f464f581a9b87017d70ce0b058d9 |
c0ce9e6150e9d7a19455db82f3318b4c |
Changes since v1.1.1
Major Themes
- Significant scale improvements. Increased cluster scale by 400% to 1000 nodes with 30,000 pods per cluster.
Kubelet supports 100 pods per node with 4x reduced system overhead.
- Simplified application deployment and management.
- Dynamic Configuration (ConfigMap API in the core API group) enables application
configuration to be stored as a Kubernetes API object and pulled dynamically on
container startup, as an alternative to baking in command-line flags when a
container is built.
- Turnkey Deployments (Deployment API (Beta) in the Extensions API group)
automate deployment and rolling updates of applications, specified
declaratively. It handles versioning, multiple simultaneous rollouts,
aggregating status across all pods, maintaining application availability, and
rollback.
- Automated cluster management:
- Kubernetes clusters can now span zones within a cloud provider. Pods from a
service will be automatically spread across zones, enabling applications to
tolerate zone failure.
- Simplified way to run a container on every node (DaemonSet API (Beta) in the
Extensions API group): Kubernetes can schedule a service (such as a logging
agent) that runs one, and only one, pod per node.
- TLS and L7 support (Ingress API (Beta) in the Extensions API group): Kubernetes
is now easier to integrate into custom networking environments by supporting
TLS for secure communication and L7 http-based traffic routing.
- Graceful Node Shutdown (aka drain) - The new “kubectl drain” command gracefully
evicts pods from nodes in preparation for disruptive operations like kernel
upgrades or maintenance.
- Custom Metrics for Autoscaling (HorizontalPodAutoscaler API in the Autoscaling
API group): The Horizontal Pod Autoscaling feature now supports custom metrics
(Alpha), allowing you to specify application-level metrics and thresholds to
trigger scaling up and down the number of pods in your application.
- New GUI (dashboard) allows you to get started quickly and enables the same
functionality found in the CLI as a more approachable and discoverable way of
interacting with the system. Note: the GUI is enabled by default in 1.2 clusters.
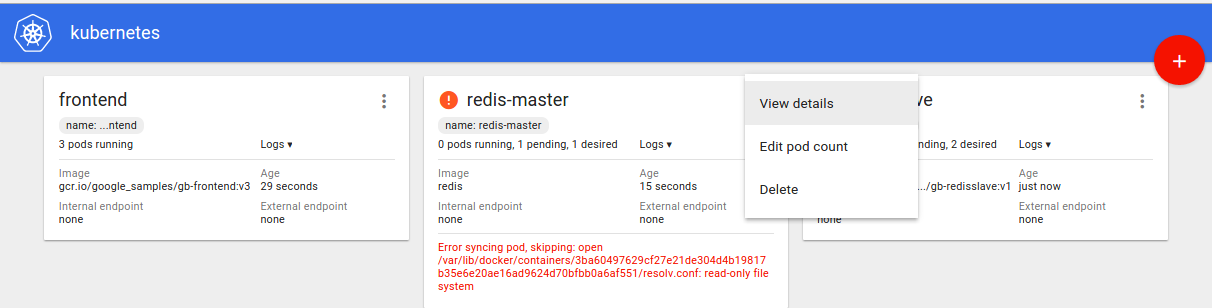
Other notable improvements
- Job was Beta in 1.1 and is GA in 1.2 .
apiVersion: batch/v1 is now available. You now do not need to specify the .spec.selector field — a unique selector is automatically generated for you.- The previous version,
apiVersion: extensions/v1beta1, is still supported. Even if you roll back to 1.1, the objects created using
the new apiVersion will still be accessible, using the old version. You can
continue to use your existing JSON and YAML files until you are ready to switch
to batch/v1. We may remove support for Jobs with apiVersion: extensions/v1beta1 in 1.3 or 1.4.
- HorizontalPodAutoscaler was Beta in 1.1 and is GA in 1.2 .
apiVersion: autoscaling/v1 is now available. Changes in this version are:
- Field CPUUtilization which was a nested structure CPUTargetUtilization in
HorizontalPodAutoscalerSpec was replaced by TargetCPUUtilizationPercentage
which is an integer.
- ScaleRef of type SubresourceReference in HorizontalPodAutoscalerSpec which
referred to scale subresource of the resource being scaled was replaced by
ScaleTargetRef which points just to the resource being scaled.
- In extensions/v1beta1 if CPUUtilization in HorizontalPodAutoscalerSpec was not
specified it was set to 80 by default while in autoscaling/v1 HPA object
without TargetCPUUtilizationPercentage specified is a valid object. Pod
autoscaler controller will apply a default scaling policy in this case which is
equivalent to the previous one but may change in the future.
- The previous version,
apiVersion: extensions/v1beta1, is still supported. Even if you roll back to 1.1, the objects created using
the new apiVersions will still be accessible, using the old version. You can
continue to use your existing JSON and YAML files until you are ready to switch
to autoscaling/v1. We may remove support for HorizontalPodAutoscalers with apiVersion: extensions/v1beta1 in 1.3 or 1.4.
- Kube-Proxy now defaults to an iptables-based proxy. If the --proxy-mode flag is
specified while starting kube-proxy (‘userspace’ or ‘iptables’), the flag value
will be respected. If the flag value is not specified, the kube-proxy respects
the Node object annotation: ‘net.beta.kubernetes.io/proxy-mode’. If the
annotation is not specified, then ‘iptables’ mode is the default. If kube-proxy
is unable to start in iptables mode because system requirements are not met
(kernel or iptables versions are insufficient), the kube-proxy will fall-back
to userspace mode. Kube-proxy is much more performant and less
resource-intensive in ‘iptables’ mode.
- Node stability can be improved by reserving resources for the base operating system using --system-reserved and --kube-reserved Kubelet flags
- Liveness and readiness probes now support more configuration parameters:
periodSeconds, successThreshold, failureThreshold
- The new ReplicaSet API (Beta) in the Extensions API group is similar to
ReplicationController, but its selector is more general (supports set-based selector; whereas ReplicationController
only supports equality-based selector).
- Scale subresource support is now expanded to ReplicaSets along with
ReplicationControllers and Deployments. Scale now supports two different types
of selectors to accommodate both equality-based selectors supported by ReplicationControllers and set-based selectors supported by Deployments and ReplicaSets.
- “kubectl run” now produces Deployments (instead of ReplicationControllers) and
Jobs (instead of Pods) by default.
- Pods can now consume Secret data in environment variables and inject those
environment variables into a container’s command-line args.
- Stable version of Heapster which scales up to 1000 nodes: more metrics, reduced
latency, reduced cpu/memory consumption (~4mb per monitored node).
- Pods now have a security context which allows users to specify:
- attributes which apply to the whole pod:
- User ID
- Whether all containers should be non-root
- Supplemental Groups
- FSGroup - a special supplemental group
- SELinux options
- If a pod defines an FSGroup, that Pod’s system (emptyDir, secret, configMap,
etc) volumes and block-device volumes will be owned by the FSGroup, and each
container in the pod will run with the FSGroup as a supplemental group
- Volumes that support SELinux labelling are now automatically relabeled with the
Pod’s SELinux context, if specified
- A stable client library release_1_2 is added. The library is here, and detailed doc is here. We will keep the interface of this go client stable.
- New Azure File Service Volume Plugin enables mounting Microsoft Azure File
Volumes (SMB 2.1 and 3.0) into a Pod. See example for details.
- Logs usage and root filesystem usage of a container, volumes usage of a pod and node disk usage are exposed through Kubelet new metrics API.
Experimental Features
- Dynamic Provisioning of PersistentVolumes: Kubernetes previously required all
volumes to be manually provisioned by a cluster administrator before use. With
this feature, volume plugins that support it (GCE PD, AWS EBS, and Cinder) can
automatically provision a PersistentVolume to bind to an unfulfilled
PersistentVolumeClaim.
- Run multiple schedulers in parallel, e.g. one or more custom schedulers
alongside the default Kubernetes scheduler, using pod annotations to select
among the schedulers for each pod. Documentation is here, design doc is here.
- More expressive node affinity syntax, and support for “soft” node affinity.
Node selectors (to constrain pods to schedule on a subset of nodes) now support
the operators {
In, NotIn, Exists, DoesNotExist, Gt, Lt} instead of just conjunction of exact match on node label values. In
addition, we’ve introduced a new “soft” kind of node selector that is just a
hint to the scheduler; the scheduler will try to satisfy these requests but it
does not guarantee they will be satisfied. Both the “hard” and “soft” variants
of node affinity use the new syntax. Documentation is here (see section “Alpha feature in Kubernetes v1.2: Node Affinity“). Design doc is here.
- A pod can specify its own Hostname and Subdomain via annotations (
pod.beta.kubernetes.io/hostname, pod.beta.kubernetes.io/subdomain). If the Subdomain matches the name of a headless service in the same namespace, a DNS A record is also created for the pod’s FQDN. More
details can be found in the DNS README. Changes were introduced in PR #20688.
- New SchedulerExtender enables users to implement custom
out-of-(the-scheduler)-process scheduling predicates and priority functions,
for example to schedule pods based on resources that are not directly managed
by Kubernetes. Changes were introduced in PR #13580. Example configuration and documentation is available here. This is an alpha feature and may not be supported in its current form at beta
or GA.
- New Flex Volume Plugin enables users to use out-of-process volume plugins that
are installed to “/usr/libexec/kubernetes/kubelet-plugins/volume/exec/” on
every node, instead of being compiled into the Kubernetes binary. See example for details.
- vendor volumes into a pod. It expects vendor drivers are installed in the
volume plugin path on each kubelet node. This is an alpha feature and may
change in future.
- Kubelet exposes a new Alpha metrics API - /stats/summary in a user friendly format with reduced system overhead. The measurement is done in PR #22542.
Action required
- Docker v1.9.1 is officially recommended. Docker v1.8.3 and Docker v1.10 are
supported. If you are using an older release of Docker, please upgrade. Known
issues with Docker 1.9.1 can be found below.
- CPU hardcapping will be enabled by default for containers with CPU limit set,
if supported by the kernel. You should either adjust your CPU limit, or set CPU
request only, if you want to avoid hardcapping. If the kernel does not support
CPU Quota, NodeStatus will contain a warning indicating that CPU Limits cannot
be enforced.
- The following applies only if you use the Go language client (
/pkg/client/unversioned) to create Job by defining Go variables of type "k8s.io/kubernetes/pkg/apis/extensions".Job). We think this is not common, so if you are not sure what this means, you probably aren't doing this. If
you do this, then, at the time you re-vendor the "k8s.io/kubernetes/" code, you will need to set job.Spec.ManualSelector = true, or else set job.Spec.Selector = nil. Otherwise, the jobs you create may be rejected. See Specifying your own pod selector.
- Deployment was Alpha in 1.1 (though it had apiVersion extensions/v1beta1) and
was disabled by default. Due to some non-backward-compatible API changes, any
Deployment objects you created in 1.1 won’t work with in the 1.2 release.
- Before upgrading to 1.2, delete all Deployment alpha-version resources, including the Replication Controllers and Pods the Deployment manages. Then
create Deployment Beta resources after upgrading to 1.2. Not deleting the
Deployment objects may cause the deployment controller to mistakenly match
other pods and delete them, due to the selector API change.
- Client (kubectl) and server versions must match (both 1.1 or both 1.2) for any
Deployment-related operations.
- Behavior change:
- Deployment creates ReplicaSets instead of ReplicationControllers.
- Scale subresource now has a new
targetSelector field in its status. This field supports the new set-based selectors supported
by Deployments, but in a serialized format.
- Spec change:
- Deployment’s selector is now more general (supports set-based selector; it only supported
equality-based selector in 1.1).
- .spec.uniqueLabelKey is removed -- users can’t customize unique label key --
and its default value is changed from
“deployment.kubernetes.io/podTemplateHash” to “pod-template-hash”.
- .spec.strategy.rollingUpdate.minReadySeconds is moved to .spec.minReadySeconds
- DaemonSet was Alpha in 1.1 (though it had apiVersion extensions/v1beta1) and
was disabled by default. Due to some non-backward-compatible API changes, any
DaemonSet objects you created in 1.1 won’t work with in the 1.2 release.
- Before upgrading to 1.2, delete all DaemonSet alpha-version resources. If you do not want to disrupt the pods, use kubectl delete daemonset
--cascade=false. Then create DaemonSet Beta resources after upgrading to 1.2.
- Client (kubectl) and server versions must match (both 1.1 or both 1.2) for any
DaemonSet-related operations.
- Behavior change:
- DaemonSet pods will be created on nodes with .spec.unschedulable=true and will
not be evicted from nodes whose Ready condition is false.
- Updates to the pod template are now permitted. To perform a rolling update of a
DaemonSet, update the pod template and then delete its pods one by one; they
will be replaced using the updated template.
- Spec change:
- DaemonSet’s selector is now more general (supports set-based selector; it only supported
equality-based selector in 1.1).
- Running against a secured etcd requires these flags to be passed to
kube-apiserver (instead of --etcd-config):
- --etcd-certfile, --etcd-keyfile (if using client cert auth)
- --etcd-cafile (if not using system roots)
- As part of preparation in 1.2 for adding support for protocol buffers (and the
direct YAML support in the API available today), the Content-Type and Accept
headers are now properly handled as per the HTTP spec. As a consequence, if
you had a client that was sending an invalid Content-Type or Accept header to
the API, in 1.2 you will either receive a 415 or 406 error.
The only client
this is known to affect is curl when you use -d with JSON but don't set a
content type, helpfully sends "application/x-www-urlencoded", which is not
correct.
Other client authors should double check that you are sending proper
accept and content type headers, or set no value (in which case JSON is the
default).
An example using curl:
curl -H "Content-Type: application/json" -XPOST -d
'{"apiVersion":"v1","kind":"Namespace","metadata":{"name":"kube-system"}}' "http://127.0.0.1:8080/api/v1/namespaces"
- The version of InfluxDB is bumped from 0.8 to 0.9 which means storage schema
change. More details here.
- We have renamed “minions” to “nodes”. If you were specifying NUM_MINIONS or
MINION_SIZE to kube-up, you should now specify NUM_NODES or NODE_SIZE.
Known Issues
- Paused deployments can't be resized and don't clean up old ReplicaSets.
- Minimum memory limit is 4MB. This is a docker limitation
- Minimum CPU limits is 10m. This is a Linux Kernel limitation
- “kubectl rollout undo” (i.e. rollback) will hang on paused deployments, because
paused deployments can’t be rolled back (this is expected), and the command
waits for rollback events to return the result. Users should use “kubectl
rollout resume” to resume a deployment before rolling back.
- “kubectl edit ” will open the editor multiple times, once for each
resource in the list.
- If you create HPA object using autoscaling/v1 API without specifying
targetCPUUtilizationPercentage and read it using kubectl it will print default
value as specified in extensions/v1beta1 (see details in #23196).
- If a node or kubelet crashes with a volume attached, the volume will remain
attached to that node. If that volume can only be attached to one node at a
time (GCE PDs attached in RW mode, for example), then the volume must be
manually detached before Kubernetes can attach it to other nodes.
- If a volume is already attached to a node any subsequent attempts to attach it
again (due to kubelet restart, for example) will fail. The volume must either
be manually detached first or the pods referencing it deleted (which would
trigger automatic volume detach).
- In very large clusters it may happen that a few nodes won’t register in API
server in a given timeframe for whatever reasons (networking issue, machine
failure, etc.). Normally when kube-up script will encounter even one NotReady
node it will fail, even though the cluster most likely will be working. We
added an environmental variable to kube-up ALLOWED_NOTREADY_NODES that
defines the number of nodes that if not Ready in time won’t cause kube-up
failure.
- “kubectl rolling-update” only supports Replication Controllers (it doesn’t
support Replica Sets). It’s recommended to use Deployment 1.2 with “kubectl
rollout” commands instead, if you want to rolling update Replica Sets.
- When live upgrading Kubelet to 1.2 without draining the pods running on the node,
the containers will be restarted by Kubelet (see details in #23104).
Docker Known Issues
1.9.1
- Listing containers can be slow at times which will affect kubelet performance.
More information here
- Docker daemon restarts can fail. Docker checkpoints have to deleted between
restarts. More information here
- Pod IP allocation-related issues. Deleting the docker checkpoint prior to
restarting the daemon alleviates this issue, but hasn’t been verified to
completely eliminate the IP allocation issue. More information here
- Daemon becomes unresponsive (rarely) due to kernel deadlocks. More information here
Provider-specific Notes
Various
Core changes:
- Support for load balancers with source ranges
AWS
Core changes:
- Support for ELBs with complex configurations: better subnet selection with
multiple subnets, and internal ELBs
- Support for VPCs with private dns names
- Multiple fixes to EBS volume mounting code for robustness, and to support
mounting the full number of AWS recommended volumes.
- Multiple fixes to avoid hitting AWS rate limits, and to throttle if we do
- Support for the EC2 Container Registry (currently in us-east-1 only)
With kube-up:
- Automatically install updates on boot & reboot
- Use optimized image based on Jessie by default
- Add support for Ubuntu Wily
- Master is configured with automatic restart-on-failure, via CloudWatch
- Bootstrap reworked to be more similar to GCE; better supports reboots/restarts
- Use an elastic IP for the master by default
- Experimental support for node spot instances (set NODE_SPOT_PRICE=0.05)
GCE
- Ubuntu Trusty support added
Please see the Releases Page for older releases.